A .WAV With A Payload
There have been reports of threat actors using a .wav file as a vector for malware.
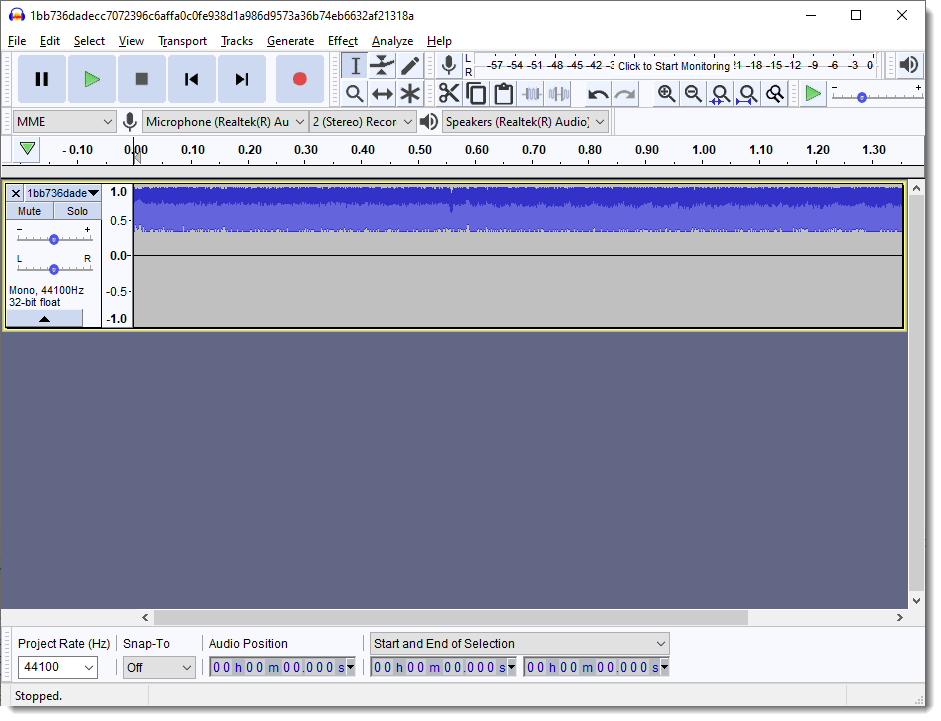
It's a proper .wav file, but they didn't use staganography. The .wav file will play, but you'll just hear noise:
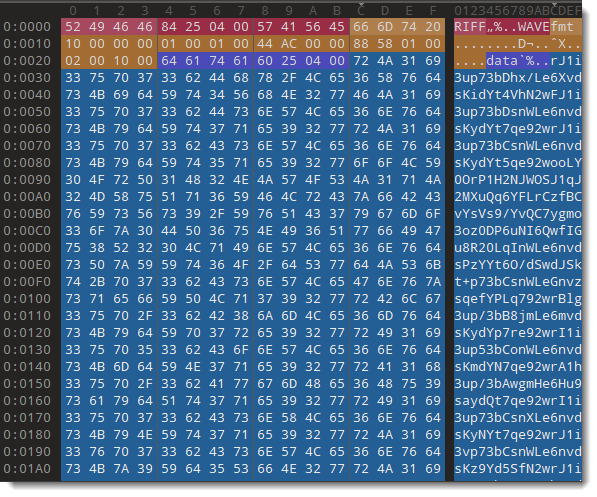
That's because the TAs have just replaced the bytes that encode the sound with the BASE64 representation of their payload:
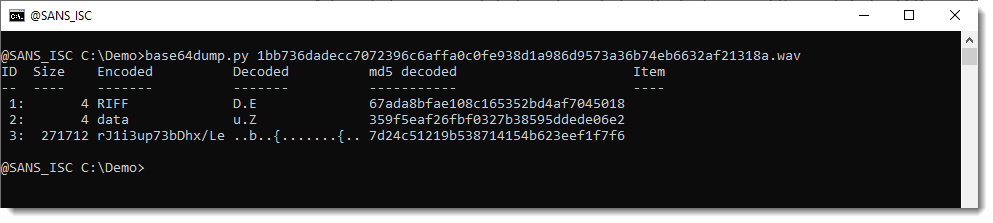
Thus I don't need a .wav parser to extract the encoded payload, I can just use my base64dump.py tool:
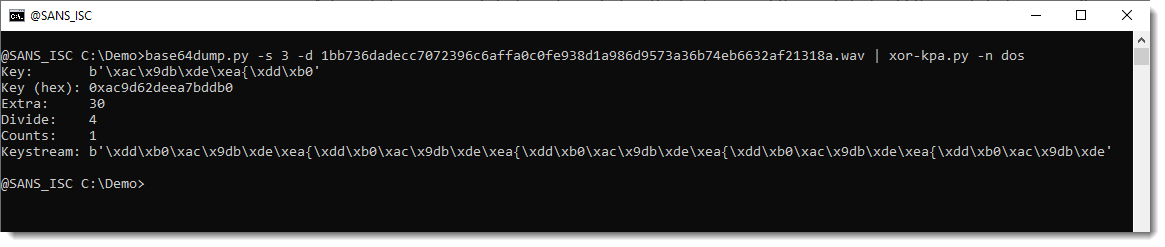
The BASE64-decoded payload is an XOR-encoded PE file. So I don't need to make a custom decoder, I can just perform a known-plaintext attack looking for the DOS header with my xor-kpa.py tool:
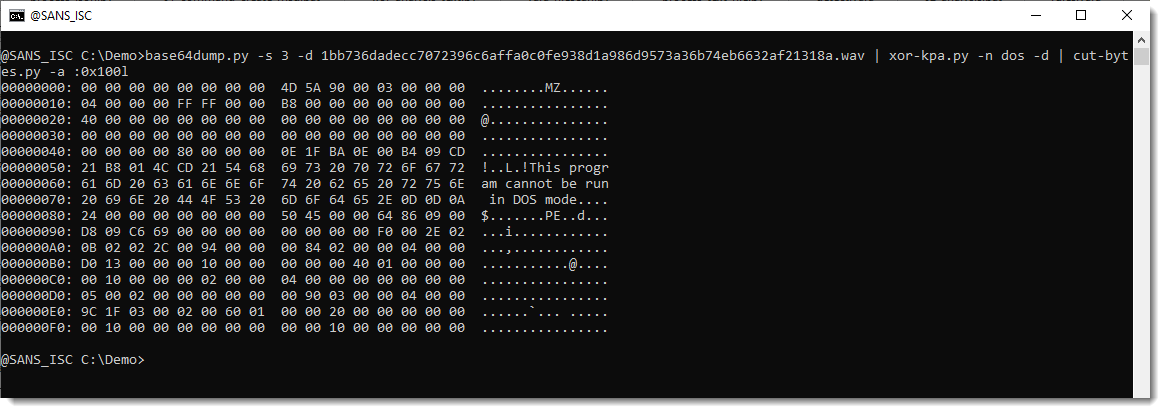
The XOR key was found. Thus we can easily dump the decoded PE file and see the MZ header at position 0x08 and a bit further down the DOS header we used in the known-plaintext-attack:
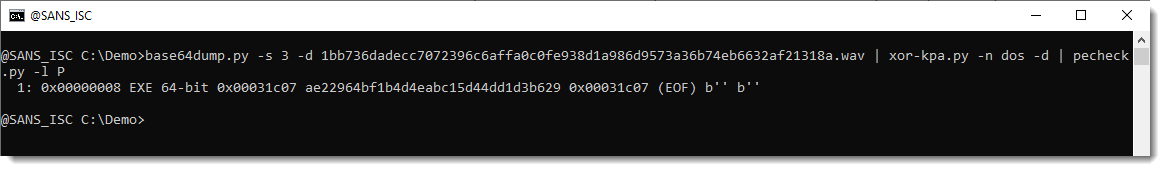
And my tool pecheck.py can extract an analyse the sample:
Didier Stevens
Senior handler
blog.DidierStevens.com


Comments