Phishing to Rural America Leads to Six-figure Wire Fraud Losses
We often focus on malware and hacking in terms of the tools the criminals use, but often good old-fashioned deception is simple enough. A recent case I worked on involves phishing sent to rural real estate professionals (law firms, title companies, realtors, etc). It is particularly effective on targets that use the various web-mail / free e-mail services.
They state by compromising one account, mine the address book for related contacts and purport to send an email about closing documents to their various contacts. Since the pretext is entirely expected, no one is overtly suspicious at this stage. The email ultimately directs to a site like this:
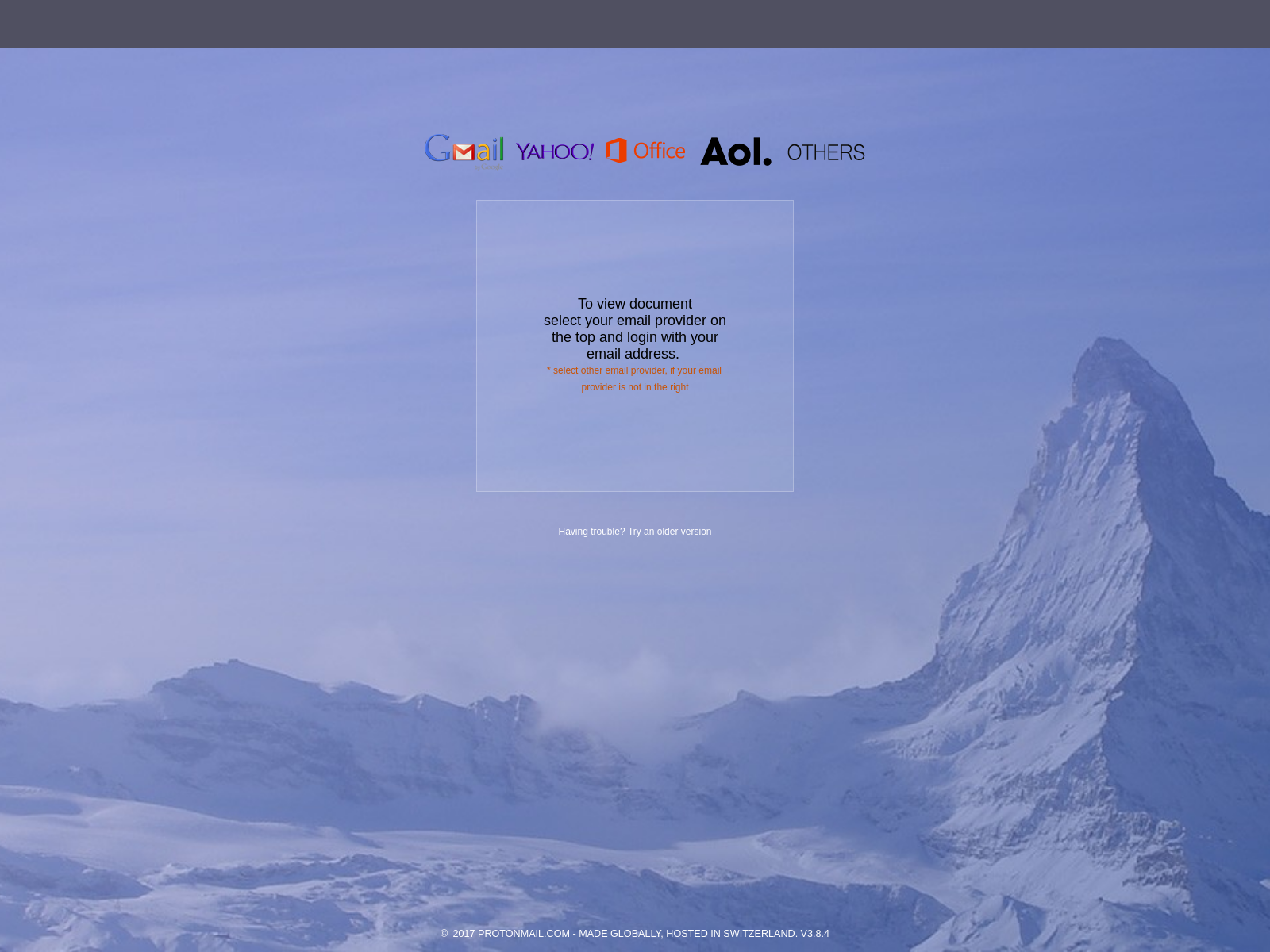
In essence, to retrieve the "sensitive documents" you need to give it your e-mail password. Superficially, it seems reasonable, but in reality it's good old fashioned information theft. The enter their credentials that are stored in a .php flat files saved on the compromised server that is hosting the content. (I was able to retrieve those credentials and pass them on for victim notification).
From there, the attacker repeates the process, using the address book to mine for more contacts and to send more e-mails. Additionally, they put forwarding rules in the e-mail based on a variety of key words looking for an appropriate transaction where they send fake wiring instructions that banks eventually honor where hard currency is sent to a money mule account and the money is then sent along. Since you only have 24 hours more or less to stop such transactions, but it often takes days to notice, the money is long gone and recovery is impossible. In the case I was called in to help, the loss was just under $200,000 to a rural client.
For big transactions, it pays to do some sort of out-of-band verification. A phone call from realtor to client to say "I just set you wiring instructions, did you receive them? Can you confirm the account and routing information?" or for that matter, from the end clients.
These kinds of fraud are all highly manual, but considering the pay day, it's worth it.
Virustotal and urlscan.io both had intel on the domains in question and modern & updates browsers also flagged the page. We have defenses and the intelligence, we need to do better to bring it down to small firms and private individuals.
Know any good browser plug-ins you recommend to friends and family to prevent phishing?
--
John Bambenek
bambenek \at\ gmail /dot/ com
Fidelis Cybersecurity


Comments
Anonymous
Jan 4th 2018
8 years ago
Not really a browser plug-in, but opendns on the router/dhcp server (probably one in the same) will block a lot of that.
Anonymous
Jan 4th 2018
8 years ago
Not really a browser plug-in, but opendns on the router/dhcp server (probably one in the same) will block a lot of that.[/quote]
Yes, a browser plug-in for Firefox: NoScript! It is a very apt protection against phishing. If you keep JS forbidden by default, a phishing site (hosted on an arbitrary domain) will most probably not work. Or do you know a phishing site that works w/o JS?
Anonymous
Jan 5th 2018
8 years ago
Anonymous
Jan 5th 2018
8 years ago