Dridex malspam seen on Monday 2017-04-10
Introduction
Malicious spam (malspam) pushing the Dridex banking Trojan disappeared in mid-2016, but it reappeared in January 2017 starting with a small campaign targeting UK financial institutions [1]. Since then, we've seen a handful of reporting about Dridex, but I hadn't noticed the same large-scale distribution like we saw in 2015 and 2016. At least not until recently.
Less than two weeks ago on 2017-03-30, high-volume waves of malspam pushing Dridex reappeared [2]. Because my last in-depth look at Dridex for the ISC was in January 2016 [3], I think it's high time we take a more current look at this malspam.
Thursday 2017-03-30
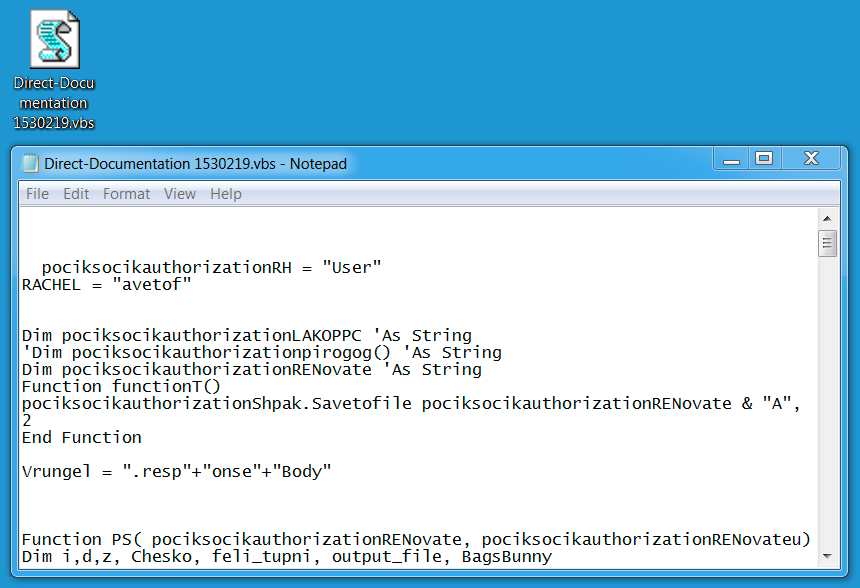
On Thursday 2017-03-30, we saw Dridex from at least two different waves of malspam [4]. In one wave of emails, attachments were zip archives containing a Visual Basic Script (.vbs) file. In the other wave, attachments were zip archives containing a Windows executable. Both attachments were double-zipped, meaning they contained a zip archive within the zip archive before you got to the malware.
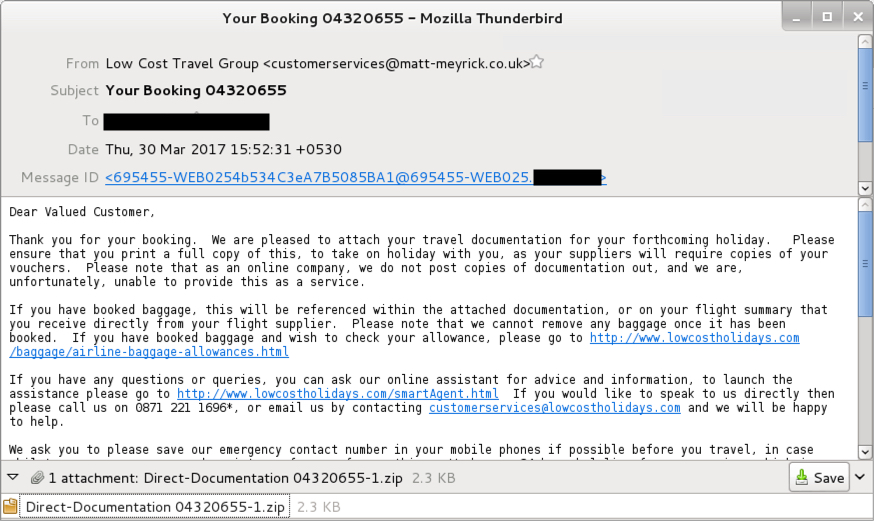
Shown above: Email from a wave of Dridex malspam on 2017-03-30.
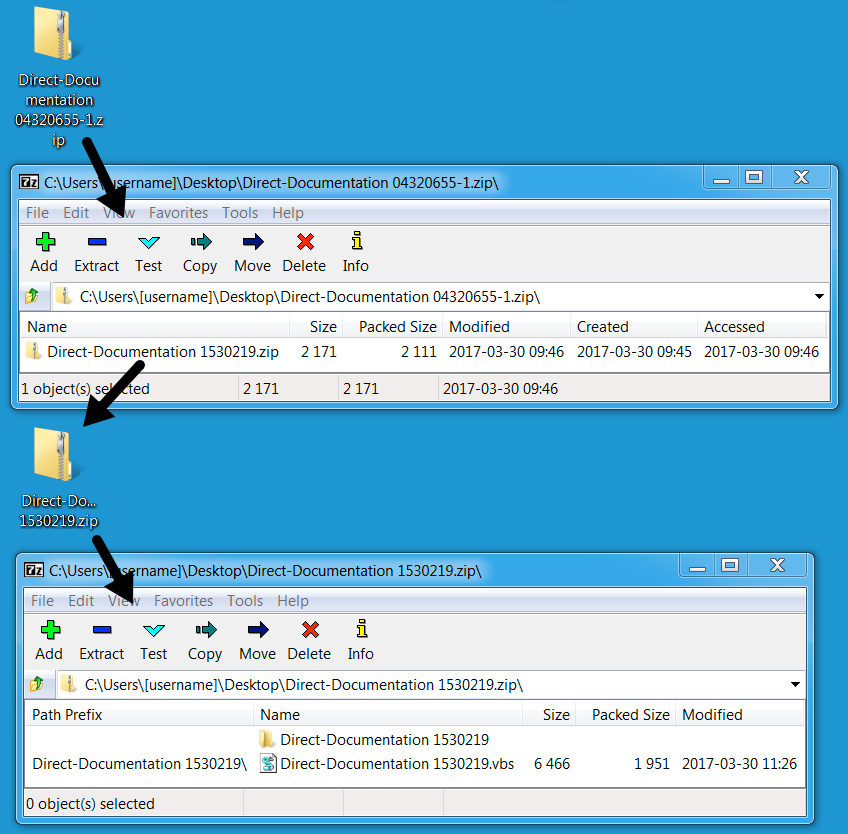
Shown above: Attachment from the above email.
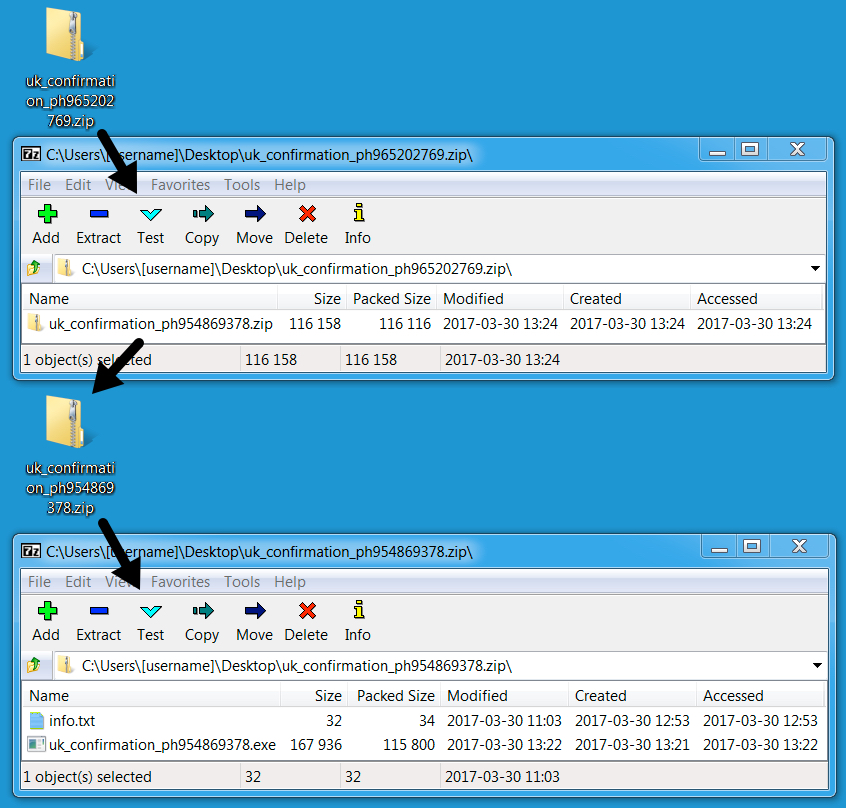
Shown above: Extracted .js file designed to download/install Dridex.

Shown above: Email from another wave of Dridex malspam on 2017-03-30.
Shown above: Attachment from the above email.
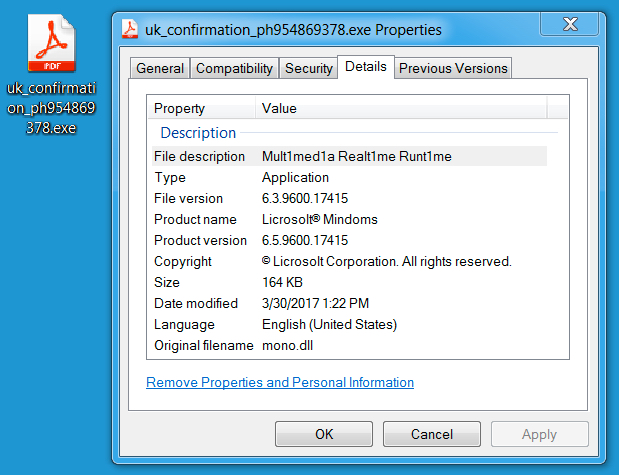
Shown above: Extracted executable (Dridex).
On Friday 2017-04-07, I saw another wave of Dridex that I didn't have time to document. Attachments were now zip archives containing Word documents. These Word documents had macros designed to download and install Dridex. Like Dridex malspam from the previous week, these archives were double-zipped.
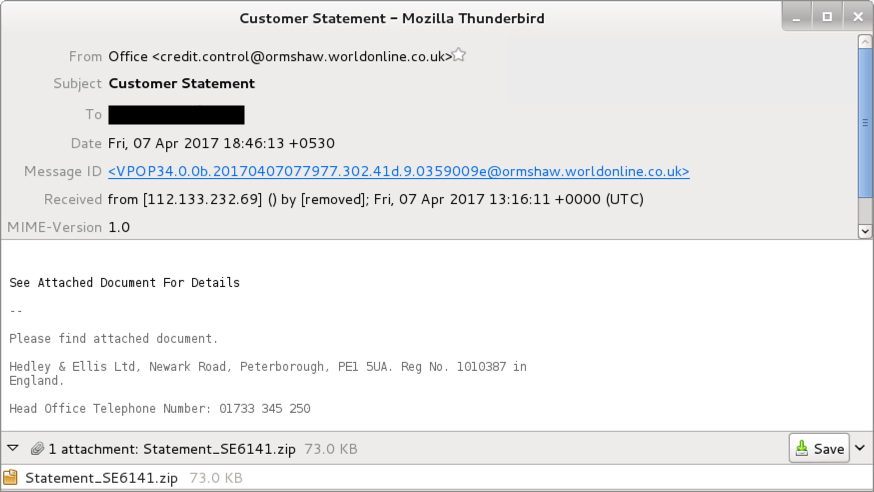
Shown above: Email from a wave of Dridex malspam on 2017-04-07.
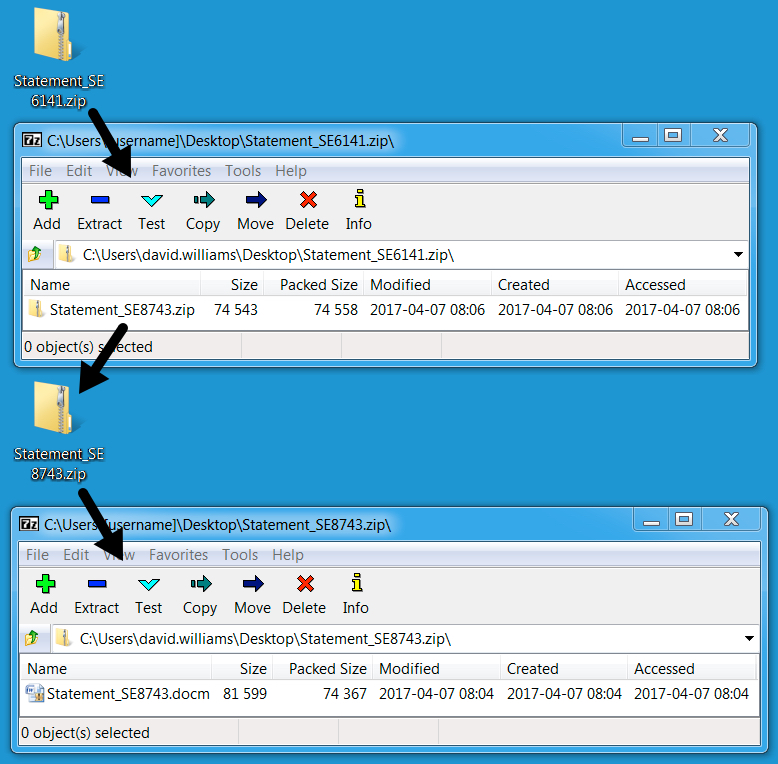
Shown above: Attachment from the above email.
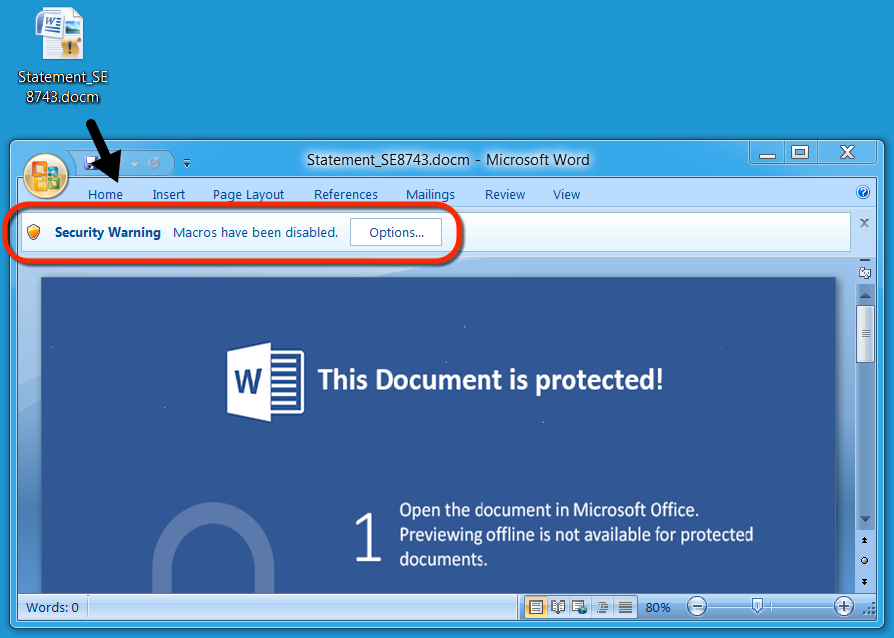
Shown above: Extracted Word document with macros designed to download/install Dridex.
Monday 2017-04-10
On Monday 2017-04-10, another wave of Dridex malspam occurred. This wave of malspam tried a new tactic. Attachments from were now PDF files with embedded Word documents. These PDF files required user action to open the Word document. Then the user had to enable macros to infect a Windows computer.
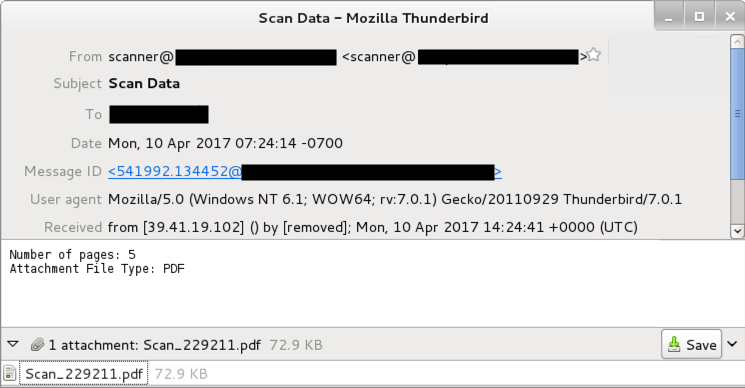
Shown above: Email from a wave of Dridex malspam on 2017-04-07.
Shown above: Opening the PDF file on a Windows host leads to the embedded Word document.
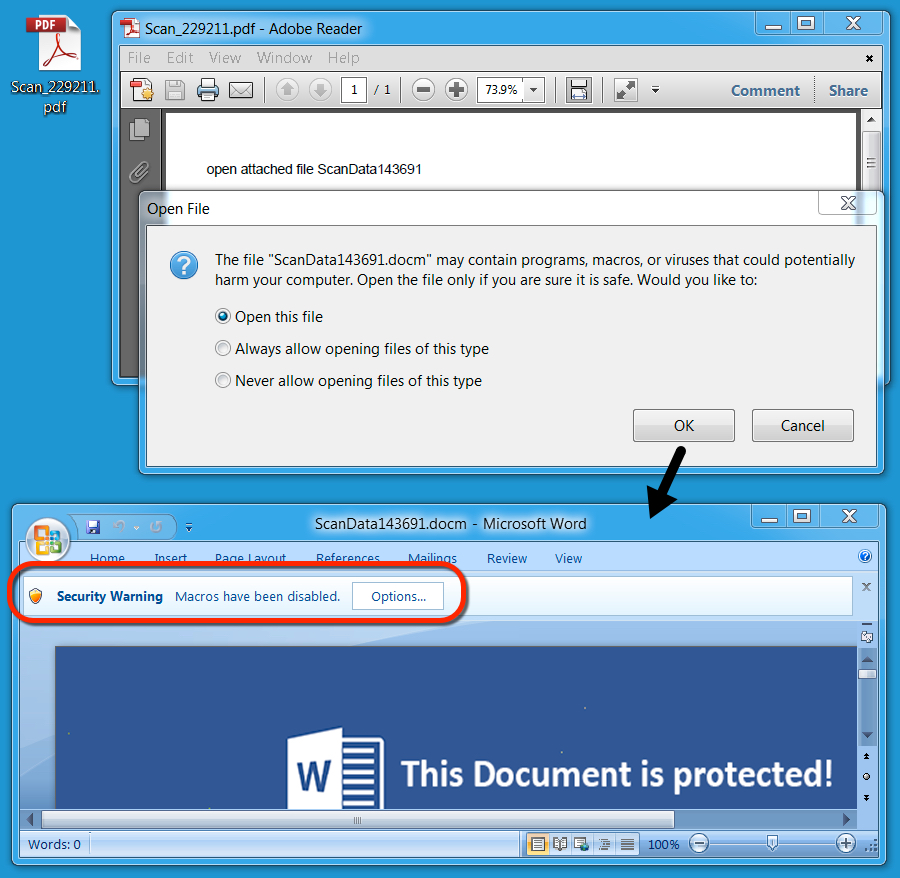
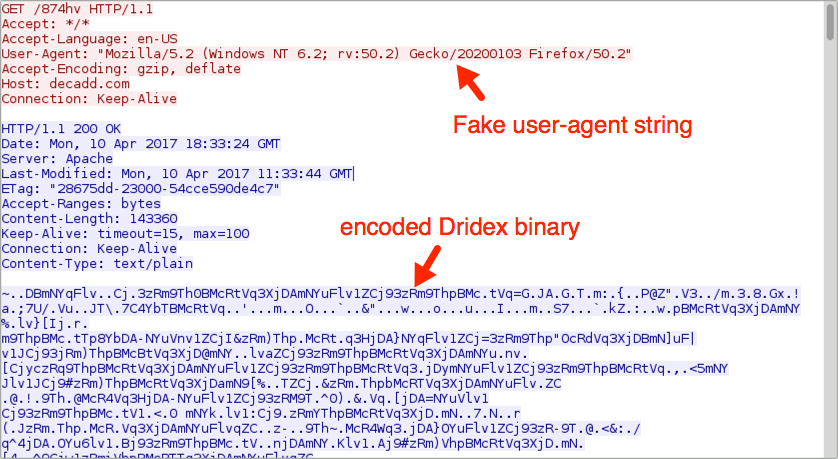
I infected a Windows host by opening one of the PDF files and enabling macros for the embedded Word document. Filtering on the traffic in Wireshark, you'll see the initial HTTP request to download Dridex. Then you'll find three different IP addresses for post-infection SSL/TLS traffic associated with Dridex.
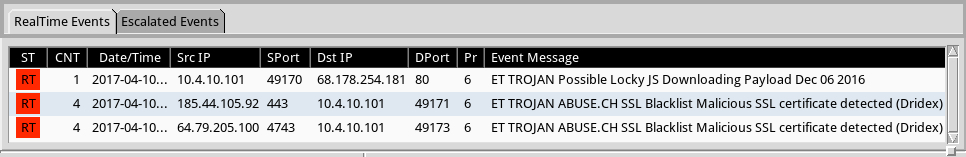
The Dridex binary was encoded while it was sent over the network. The encoded binary was saved to the Windows host at C:\Users\[username]\AppData\Local\Temp\ferbys2 where it was decoded and saved in the same directory as redchip2.exe.

Shown above: Infection traffic filtered in Wireshark: http.request or (!(tcp.port eq 80) and tcp.flags eq 0x0002).
Shown above: Alerts on the traffic using Security Onion running Suricata with the Proofpoint/ET open ruleset.
Shown above: Encoded Dridex binary retrieved by the Word macro.
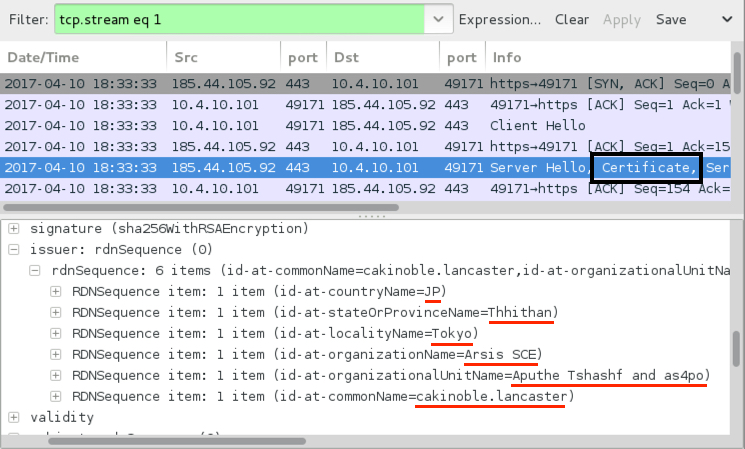
Shown above: Certificate data associated with Dridex post-infection SSL/TLS traffic.
Indicators of Compromise (IOC) from Monday 2017-04-10
The following URLs were extracted from the Word document macros seen on Monday 2017-04-10. These URLs retrieved the encoded Dridex binary. Many of these have already been taken off-line.
- 211shap.ru - GET /874hv
- anticon.net - GET /874hv
- cardoso1.com - GET /874hv
- centralsecuritybureau.com - GET /874hv
- decadd.com - GET /874hv
- designbyli.com - GET /874hv
- hiddencreek.comcastbiz.net - GET /874hv
- jheroen.nl - GET /874hv
- kapil.50webs.com - GET /874hv
- kpwc.comcastbiz.net - GET /874hv
- marinusjanssen.nl - GET /874hv
- ncdive.com - GET /874hv
- produlav.com.br - GET /874hv
- RussellYermal.com - GET /874hv
- solucionesfenix.net - GET /874hv
- super-marv.com - GET /874hv
- trans-atm.com - GET /874hv
- tserv.su - GET /874hv
- usawaterproofing.com - GET /874hv
- www.mdfond.ru - GET /874hv
Below is SSL/TLS post-infection traffic and associated certificate data from my infected Windows host on 2017-04-10:
IP address 64.79.205.100 over TCP port 4743
- countryName = ID
- stateOrProvinceName = upind0
- localityName = Jakarta
- organizationName = Tbreimem SAS
- organizationUnitName = Ptb@enc Cindusto Atoumo
- commonName = halindngofol.weadtrgtutmt.gn
IP address 185.25.184.214 over TCP port 4743
- countryName = CY
- stateOrProvinceName = Meourep Seinhadth tberese0
- localityName = Nicosia
- organizationName = Tteeran SNC
- commonName = llrrofom.fo
IP address 185.44.105.92 over TCP port 443:
- countryName = JP
- stateOrProvinceName = Thhithan
- localityName = Tokyo
- organizationName = Arsis SCE
- organizationUnitName = Aputhe Tshashf and as4po
- commonName = cakinoble.lancaster
Final words
For now, it looks like high-volume Dridex distribution through malspam is once again a feature of our current threat landscape. But how much of a threat is it?
As always, if you have a properly-configured Windows host in a well-administered environment, your risk of infection is low. But as usual, humans are the weakest link in this infection chain. If people are determined to bypass all warnings, and their systems are configured to allow it, they may very well become infected.
Emails, malware samples, and the pcap associated with 2017-04-10 Dridex malspam can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net
References
[1] FlashPoint: Dridex Banking Trojan Returns, Leverages New UAC Bypass Method
[2] Proofpoint: High-Volume Dridex Campaigns Return, First to Hit Millions Since June 2016
[3] SANS Internet Storm Center (ISC): Dridex malspam example from January 2016
[4] Malware-traffic-analysis.net: 2017-03-30 - Dridex malspam (2 waves)


Comments
According to my source [3] infection takes place when simply opening the document, i.e. before clicking on a button in order to enable execution of macro's.
Hopefully Microsoft addresses this 0day in their security updates later today.
[1] https://twitter.com/certbund/status/851724323127734272
[2] https://www.proofpoint.com/us/threat-insight/post/dridex-campaigns-millions-recipients-unpatched-microsoft-zero-day
[3] https://www.heise.de/security/meldung/Dridex-Botnetz-verteilt-millionenfach-Angriffs-Mails-auf-ungepatchte-Office-Luecke-3681553.html
Anonymous
Apr 11th 2017
9 years ago
I hope so, but wasn't the last patch-Tuesday delayed for a month? I haven't seen anything yet today, but I'll keep my fingers crossed.
I also haven't seen any Dridex malspam with the 0-day exploit yet. All I've seen are the large-scale distribution Dridex that doesn't appear to be targeted for any specific region. There's more of the same today on Tuesday 2017-04-11, just like I've already posted about with PDF attachments having embedded Word documents with malicious macros.
Anonymous
Apr 11th 2017
9 years ago
It's not yet 10 AM Pacific on the 2nd Tuesday in the current month.
Please check again, in 62 minutes. :-)
Anonymous
Apr 11th 2017
9 years ago