Campaign evolution: Hancitor changes its Word macros
Update:
Hancitor malspam was active today on 2018-12-05, and it went back to the older style of macros. Today showed 6.exe and 6.pif in the infected user's AppData\Local\Temp directory instead of werd.exe and wird.exe in the user's AppData\Roaming directory as shown in this diary. Files for today's infection with the older macros can be found here. My thanks, as always, to everyone who keeps an eye on Hancitor activity and reports about it on Twitter.
Introduction
Today's diary reviews trends in recent malicious spam (malspam) pushing Hancitor.
Background: Malspam pushing Hancitor (also known as Chanitor or Tordal) is a long-running campaign. In recent months, we've often seen waves of Hancitor malspam 2 or 3 times each week. Infections from this malspam tend to follow predictable patterns, and have ended with Ursnif as the follow-up malware since the end of October 2018 (previously it had been Zeus Panda Banker).
Recent activity: After a wave of malspam on 2018-10-29, this campaign went silent, and we saw no new Hancitor malspam for one month. Last week on Thursday 2018-11-29, Hancitor malspam returned with changes to the macro code in the associated Word documents. Hancitor is still sending Ursnif as its follow-up malware.
Today's diary reviews an infection from Hancitor malspam seen on Tuesday 2018-12-04.
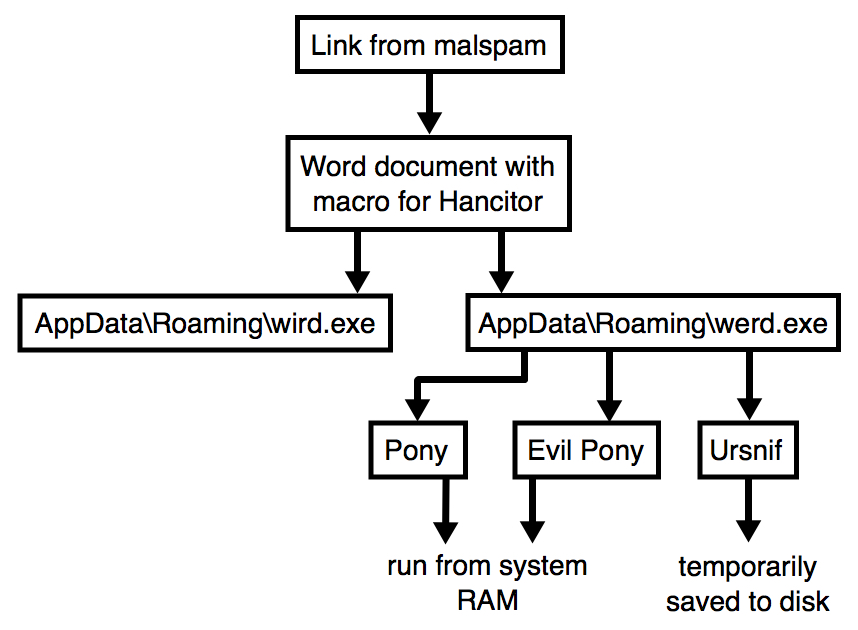
Shown above: Flow chart for the Hancitor infection on Tuesday 2018-12-04.
The malspam
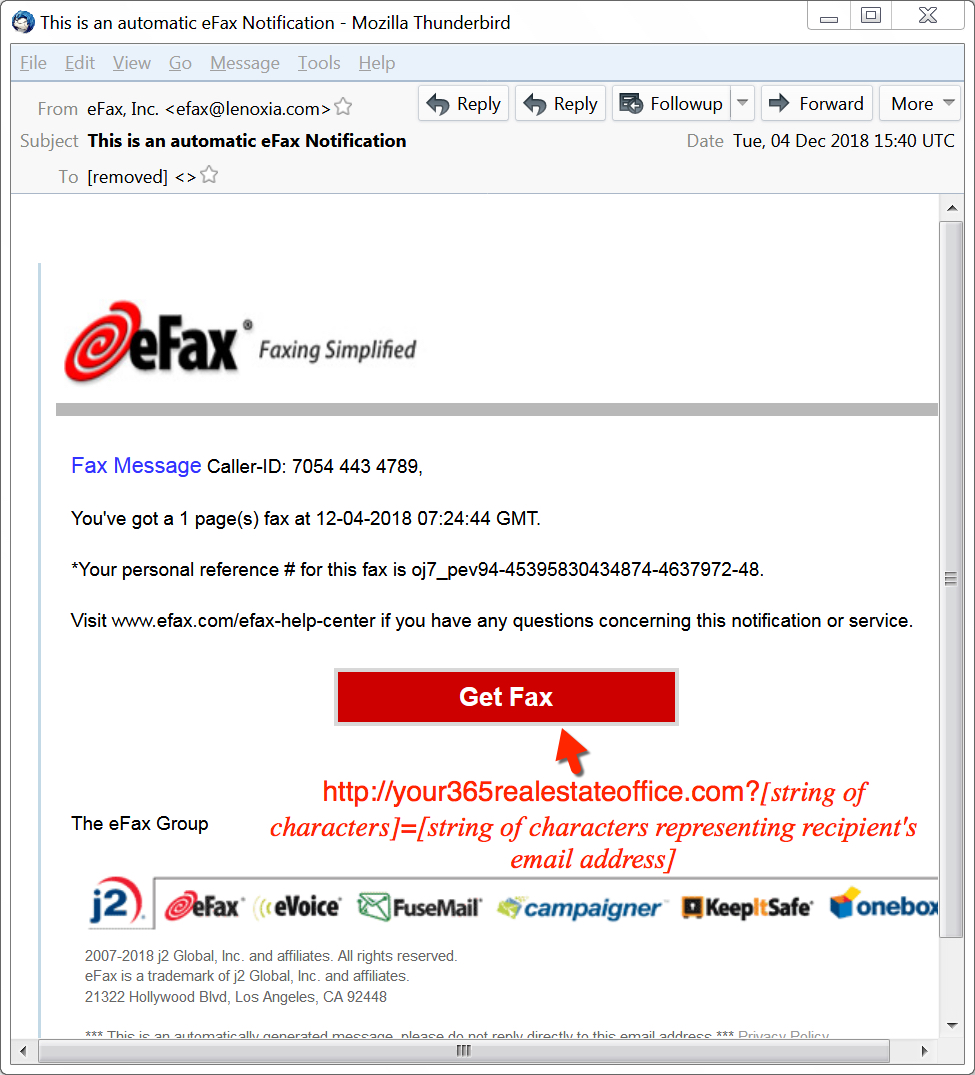
Shown above: Screen shot from an email in this malspam wave.
The email template for Tuesday's malspam was eFax-themed, which is something we've occasionally see from this campaign. No big surprises here. And the link to download a Word document follows the same pattern of ASCII characters at the end, where all characters after the = sign are an encoded string that represents the recipient's email address. I'm still not sure how to decode these strings.
Below is an example of the email headers from one of the messages on Tuesday:
Received: from lenoxia.com ([169.203.179.39]) by [removed] for [removed];
Tue, 04 Dec 2018 15:38:56 +0000 (UTC)
Date: Tue, 04 Dec 2018 08:40:58 -0700
MIME-Version: 1.0
X-Mailer: iPad Mail (11D169b)
Content-Transfer-Encoding: 7bit
Subject: This is an automatic eFax Notification
Message-ID: <1563DCE3.5F979EAC@lenoxia.com>
From: "eFax, Inc." <efax@lenoxia.com>
Content-Type: text/html;
charset="utf-8"
TO: [removed]
Reply-To: "eFax" <efax@lenoxia.com>
At first glance, the downloaded Word document looks similar to those seen in previous waves of Hancitor malspam. Victims must enable macros to infect a vulnerable Windows host. However, the macros act noticeably different than before (more on that later).

Shown above: Downloading a Word document from a link in the malspam.
Infection traffic
Infection traffic follows the same patterns we've previously seen for Hancitor, except wotj additional infection traffic for Ursnif instead of Zeus Panda Banker. In this case, I also saw Tor traffic, which might be related to the Ursnif activity. An HTTP request to amalu[.]at returned an encoded binary about 2.2 MB in size, which matched a malware binary I found on the infected Windows host for Send Safe Enterprise (SSE) spambot malware. I also saw the UDP beaconing traffic associated with SSE spambot malware.
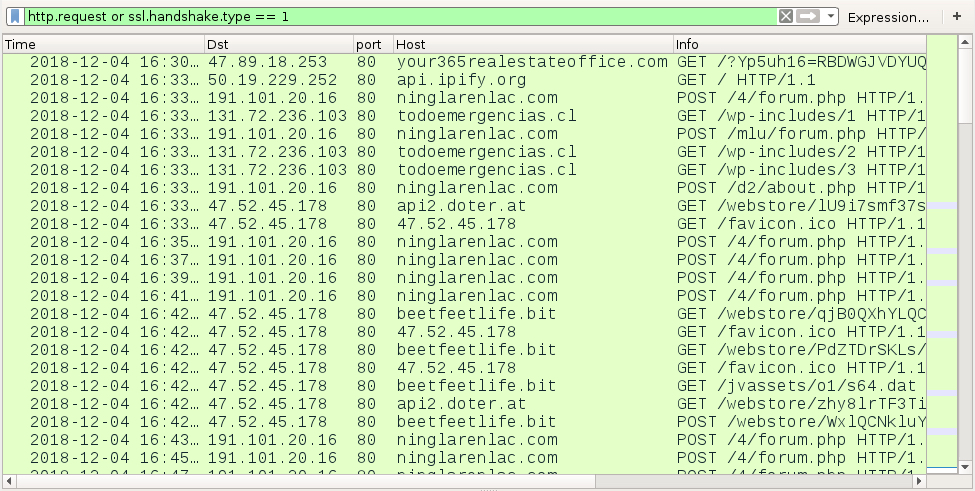
Shown above: The initial infection traffic filtered in Wireshark, showing Hancitor and Ursnif traffic.
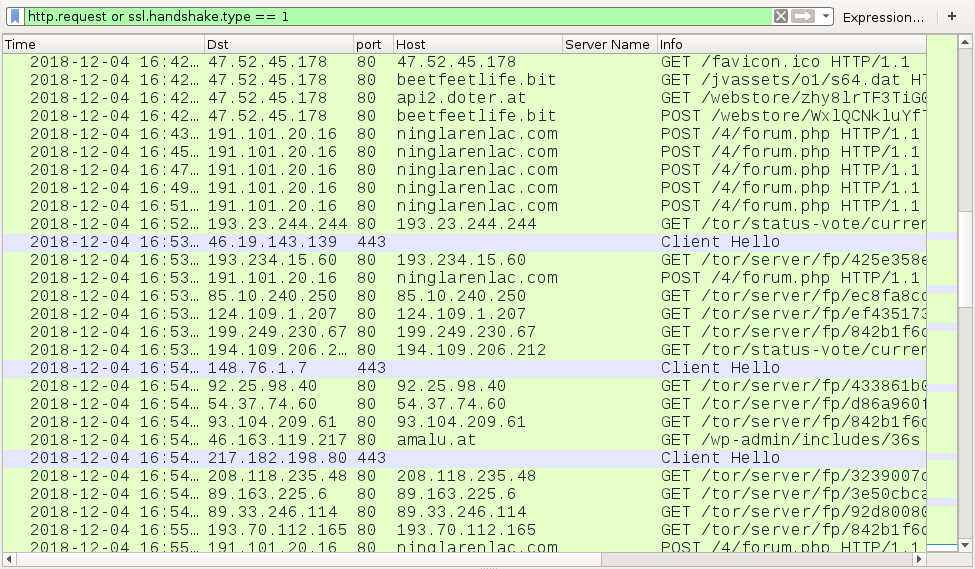
Shown above: Later in the infection, we find Tor traffic.
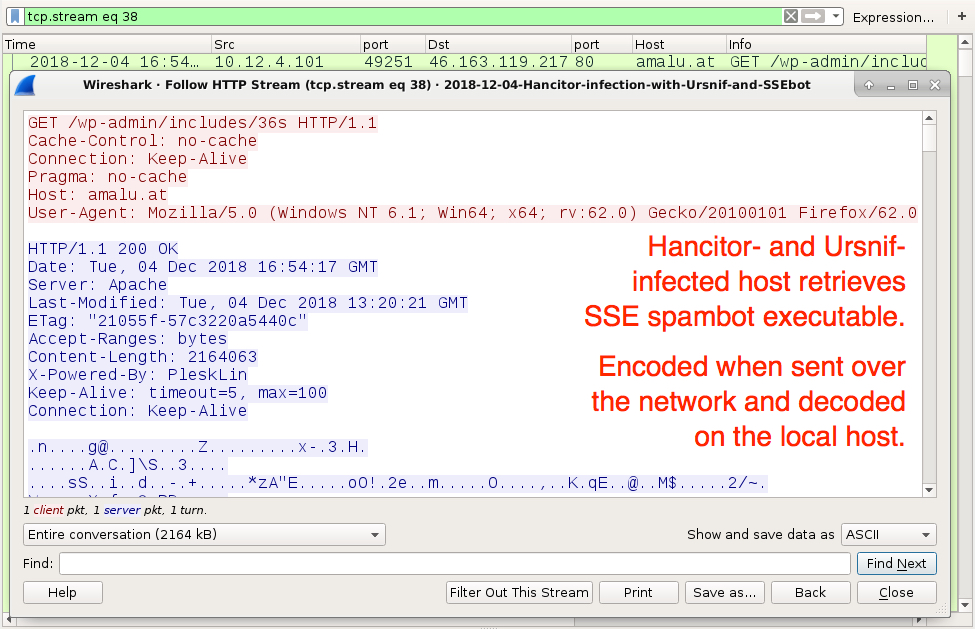
Shown above: Infected host retrieves SSE spambot executable (encoded when sent over the network).
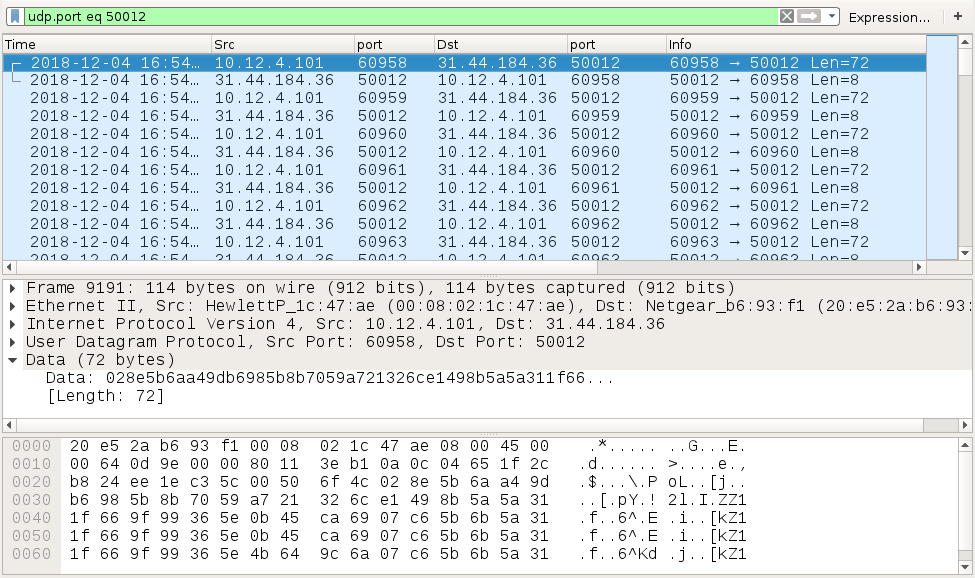
Shown above: UDP beaconing traffic caused by SSE spambot malware.
Forensics on the infected host
Unlike previous Hancitor Word docs, ever since Hancitor reappeared on 2018-11-29, the Word documents are noticeably larger, and they contain ASCII-based hex code that is decoded as two executable files dropped after enabling macros. These two executables are named werd.exe and wird.exe, and they're dropped to the user's AppData\Roaming directory. A folder also appeared in the AppData\Roaming directory with links copied from the desktop of my infected Windows host. I also saw folders named msohtmlclip and msohtmlclip1 that were created in the user's AppData\Local\Temp directory.
Ursnif was made persistent through about 14MB of ASCII code stored as Windows registry entries. This is normal for Ursnif infections, and I've exported a copy of these registry entries so people can review them. See the link at the end of this dairy to access the data.
Finally, SSE spambot malware was stored in the user's AppData\Local\Temp directory using random digits in the filename.
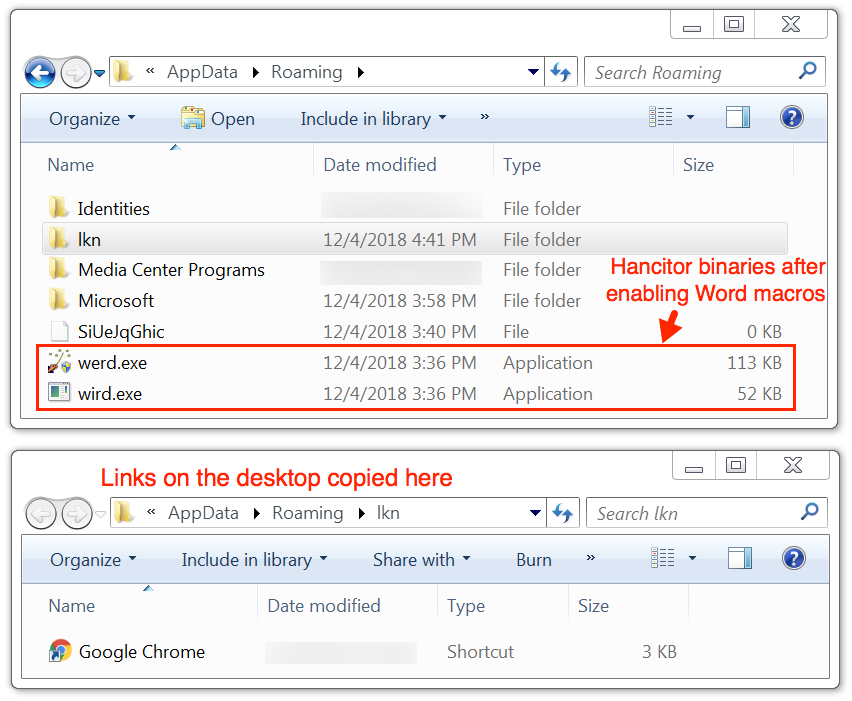
Shown above: werd.exe and word.exe dropped to the user's AppData\Local\Temp directory.

Shown above: More artifacts from the infected Windows host.

Shown above: Windows registry entries created by Ursnif on the infected Windows host.
Indicators
The following are indicators from an infected Windows host. Any malicious URLs, IP addresses, and domain names have been "de-fanged" to avoid any issues when viewing today's diary.
URL from the malspam text to download the initial Word document:
- 47.89.18[.]253 port 80 - your365realestateoffice[.]com - GET /?[string of characters]=[string of characters representing recipient's email address]
Hancitor infection traffic after enabling Word macros:
- port 80 - api.ipify.org - GET / (IP address check by the infected host, not inherently malicious)
- 191.101.20[.]16 port 80 - ninglarenlac[.]com - POST /4/forum.php
- 191.101.20[.]16 port 80 - ninglarenlac[.]com - POST /mlu/forum.php
- 191.101.20[.]16 port 80 - ninglarenlac[.]com - POST /d2/about.php
- 131.72.236[.]103 port 80 - todoemergencias[.]cl - GET /wp-includes/1
- 131.72.236[.]103 port 80 - todoemergencias[.]cl - GET /wp-includes/2
- 131.72.236[.]103 port 80 - todoemergencias[.]cl - GET /wp-includes/3
Ursnif infection traffic:
- 47.52.45[.]178 port 80 - api2.doter[.]at - GET /webstore/[long string]
- 47.52.45[.]178 port 80 - 47.52.45[.]178 - GET /favicon.ico
- 47.52.45[.]178 port 80 - beetfeetlife[.]bit - GET /webstore/[long string]
- 47.52.45[.]178 port 80 - beetfeetlife[.]bit - GET /jvassets/o1/s64.dat
Tor traffic seen after the initial Hancitor and Ursnif activity:
- various IP addresses over mostly port 80 - GET /tor/status-vote/current/consensus
- various IP addresses over mostly port 80 - GET /tor/server/fp/[long hex string]
- various IP addresses over port 443 - SSL/TLS traffic
Infected host retrieves SSE spambot malware:
- 46.163.119[.]217 port 80 - amalu[.]at - GET /wp-admin/includes/36s
UDP beacon caused by SSE spambot malware:
- 31.44.184[.]36 port 50012
Malware from an infected Windows host:
SHA256 hash: eebc056d535f2b1278df043eee776595b6526e47a6cffdc67641c165b1f5e973
- File size: 458,240 bytes
- File description: Word doc downloaded form email link, doc has macro for Hancitor
- File name: invoice_530486.doc (random digits in the file name)
SHA256 hash: ad783ca9c2bd4c9905b131d170c1dce5bad9de8b8c2d4607a8cd051021284df0
- File size: 114,690 bytes
- File description: Hancitor malware binary dropped by Word macro
- File location: C:\Users\[username]\AppData\Roaming\werd.exe
SHA256 hash: a1a0cb7e5a7239b7aa69f2d052464c201bd5082d9a8b2aac6997fda5de9a7228
- File size: 52,226 bytes
- File description: Hancitor-related executable dropped by Word macro
- File location: C:\Users\[username]\AppData\Roaming\wird.exe
SHA256 hash: 9350609c8c806a9c1a667fd53926ea85745e1da239df7f3c2aad3e3527bd48d1
- File size: 249,544 bytes
- File description: Ursnif executable retrieved by Hancitor-infected host
- File location: C:\Users\[username]\AppData\Local\Temp\BNA4D6.tmp (random characters in the file name)
SHA256 hash: 86ca2f22dd4c99b57bb9d272cd5dd91978e15853efa0c05ede8c80694a8d27a6
- File size: 2,163,976 bytes
- File description: Send Safe Enterprise (SSE) spambot malware
- File location: C:\Users\[username]\AppData\Local\Temp\1907751.exe (random digits in the file name)
Final words
3 email examples, a pcap of the infection traffic, and malware/artifacts associated with today's diary can be found here.
---
Brad Duncan
brad [at] malware-traffic-analysis.net


Comments