Alternative Ways To Perform Basic Tasks
I like to spot techniques used by malware developers to perform basic tasks. We know the lolbins[1] that are pre-installed tools used to perform malicious activities. Many lolbins are used, for example, to download some content from the Internet. Some tools are so powerful that they can also be used to perform unexpected tasks. I found an interesting blog article[2] describing how to use curl to copy files!
C:\Users\REM> curl file://c:\test\test.txt -o newfile.txt
Do you want another example? Some tools can be diverted from their regular use like ping.exe:
C:\Users\REM\Desktop>ping -n 5 127.0.0.1
This command will send five Echo-Request ICMP packets at an interval of one second so it will complete after approximately five seconds. Using ping.exe is not very discreet because a new process will be launched and can be spotted by a tool like Sysmon. Do you know a lot of non-tech people that use ping on their corporate computer?
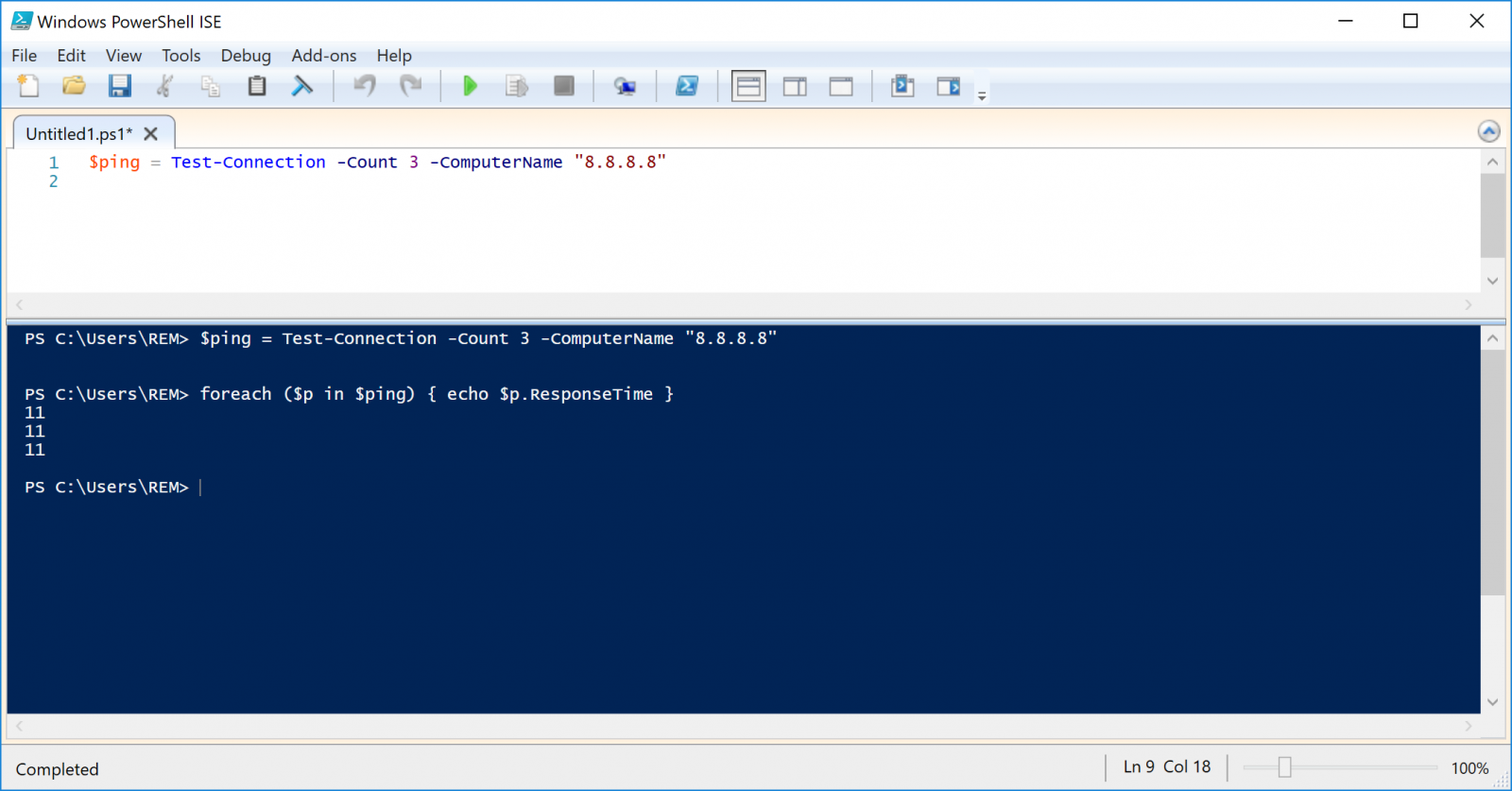
But ping.exe can be very useful for malware to detect if the computer can resolve hostnames and has Internet connectivity. Instead of using the ping command, you can use Powershell to achieve this:
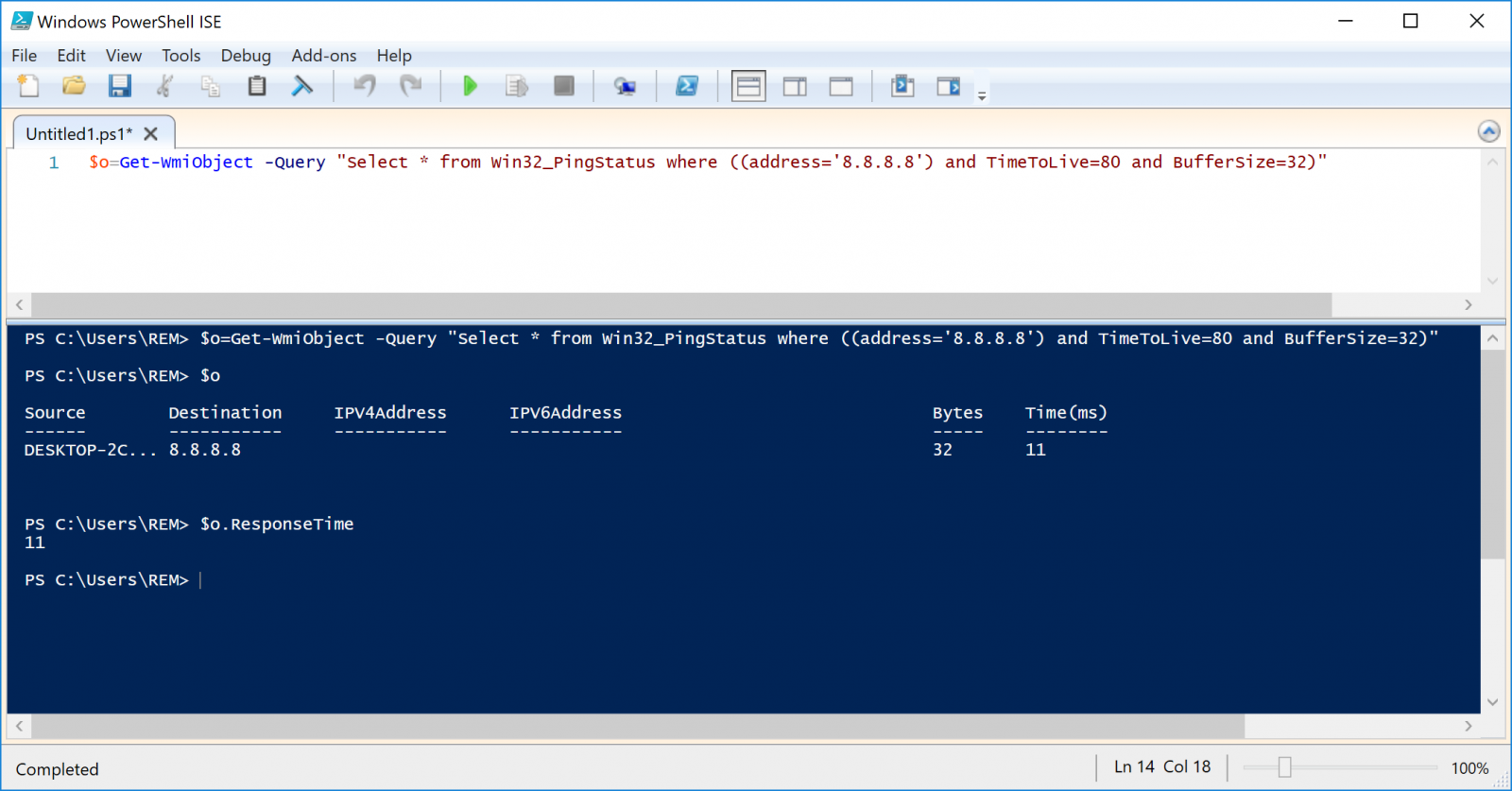
Yesterday, I found a malicious PowerShell script that uses another technique that I never saw before. This time, the technique is based on a WMI query!
Conclusion: Keep in mind that attackers can use multiple techniques to perform simple tasks and defeat your detection rules and/or controls.
If you already met other techniques, please share!
[1] https://lolbas-project.github.io
[2] https://www.hexacorn.com/blog/2021/05/02/curo-bin/
Xavier Mertens (@xme)
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments