Infostealer Embedded in a Word Document
When attackers design malicious documents, one of their challenges is to make the potential victim confident to perform dangerous actions: click on a link, disable a security feature, etc. The best example is probably VBA macros in Microsoft Office documents. Disabled by default, the attacker must make the user confident to enable them by clicking on the “yellow ribbon” on top of the document.
Yesterday I found a malicious document that implements another approach. The SHA256 is c2d55f54c26d6f73908c7138e999fadcb9a8617fea8f56cee943f93956adfa12 and the VT score is 27/59. The document has an embedded object:
remnux@remnux:/MalwareZoo/20230503$ oledump.py c2d55f54c26d6f73908c7138e999fadcb9a8617fea8f56cee943f93956adfa12.doc 1: 113 '\x01CompObj' 2: 280 '\x05DocumentSummaryInformation' 3: 408 '\x05SummaryInformation' 4: 2607 '1Table' 5: 4096 'Data' 6: 76 'ObjectPool/_1567188875/\x01CompObj' 7: O 674329 'ObjectPool/_1567188875/\x01Ole10Native' 8: 6 'ObjectPool/_1567188875/\x03ObjInfo' 9: 4142 'WordDocument'
This OLE object is definitively interesting:
remnux@remnux:/MalwareZoo/20230503$ oledump.py c2d55f54c26d6f73908c7138e999fadcb9a8617fea8f56cee943f93956adfa12.doc -s 7 |more 00000000: 15 4A 0A 00 02 00 6D 69 63 72 6F 73 6F 66 74 31 .J....microsoft1 00000010: 30 63 6F 6E 76 65 72 74 65 72 73 2E 65 78 65 00 0converters.exe. 00000020: 43 3A 5C 55 73 65 72 73 5C 44 2E 45 2E 4C 2E 4C C:\Users\D.E.L.L 00000030: 5C 44 65 73 6B 74 6F 70 5C 6D 69 63 72 6F 73 6F \Desktop\microso 00000040: 66 74 31 30 63 6F 6E 76 65 72 74 65 72 73 2E 65 ft10converters.e 00000050: 78 65 00 00 00 03 00 3E 00 00 00 43 3A 5C 55 73 xe.....>...C:\Us 00000060: 65 72 73 5C 44 2E 45 2E 4C 2E 4C 5C 41 70 70 44 ers\D.E.L.L\AppD 00000070: 61 74 61 5C 4C 6F 63 61 6C 5C 54 65 6D 70 5C 6D ata\Local\Temp\m 00000080: 69 63 72 6F 73 6F 66 74 31 30 63 6F 6E 76 65 72 icrosoft10conver 00000090: 74 65 72 73 2E 65 78 65 00 60 48 0A 00 4D 5A 90 ters.exe.`H..MZ. 000000A0: 00 03 00 00 00 04 00 00 00 FF FF 00 00 B8 00 00 ................ 000000B0: 00 00 00 00 00 40 00 00 00 00 00 00 00 00 00 00 .....@.......... 000000C0: 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 ................ 000000D0: 00 00 00 00 00 00 00 00 00 80 00 00 00 0E 1F BA ................ 000000E0: 0E 00 B4 09 CD 21 B8 01 4C CD 21 54 68 69 73 20 .....!..L.!This 000000F0: 70 72 6F 67 72 61 6D 20 63 61 6E 6E 6F 74 20 62 program cannot b 00000100: 65 20 72 75 6E 20 69 6E 20 44 4F 53 20 6D 6F 64 e run in DOS mod 00000110: 65 2E 0D 0D 0A 24 00 00 00 00 00 00 00 50 45 00 e....$.......PE.
When you open the file in a sandbox, you see this:
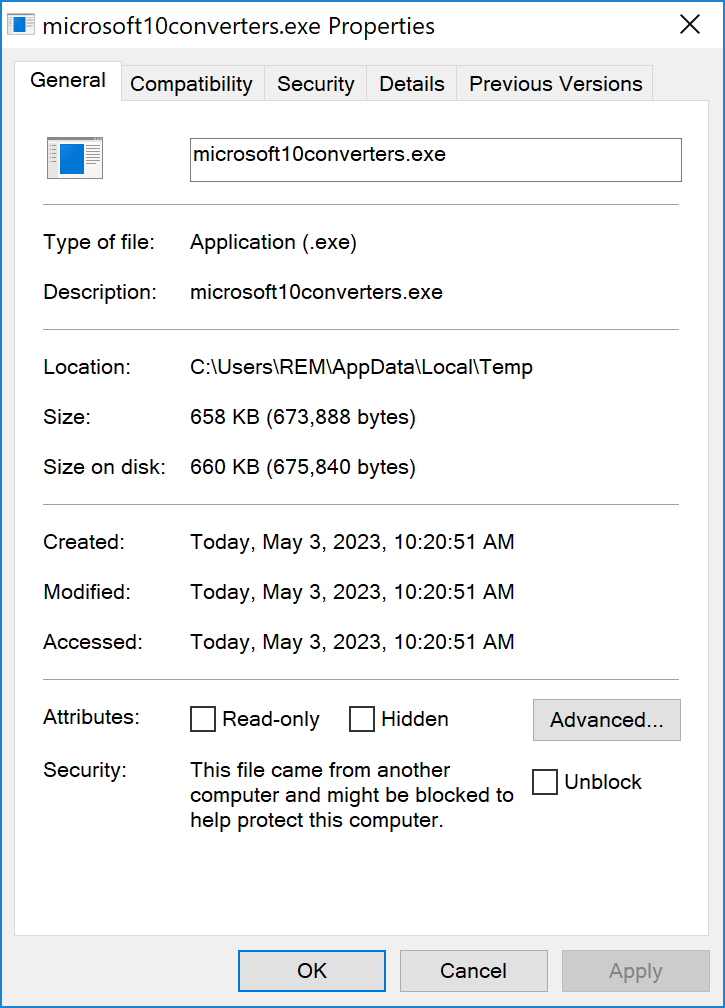
This is not a bad idea... Users could be afraid to click on the classic yellow ribbon to activate a VBA macro. Here, users are asked to double click on the object to "convert the document to normal size". The embedded object properties:
Let's extract the PE file from the document:
remnux@remnux:/MalwareZoo/20230503$ oledump.py c2d55f54c26d6f73908c7138e999fadcb9a8617fea8f56cee943f93956adfa12.doc -s 7 -e >sample.exe
The extract payload is a .Net executable[1]. It's an infostealer that exfiltrates data using the following config:
{
"flow":20,
"host":"mail.tcci.org.sa",
"port":587,
"password":"<Redacted>",
"protocol":"smtp",
"username":"fahad.s@tcci.org.sa"
}
[1] https://bazaar.abuse.ch/sample/4c312e3cce557ee17db0299bcc112699e616fb162afdadf12a41815a4a314b5c/
Xavier Mertens (@xme)
Xameco
Senior ISC Handler - Freelance Cyber Security Consultant
PGP Key


Comments